In the last month I’ve developed a real problem: All I want to do is work on security related topics.
The day after I wrote my last post I managed to gain root access to my first virtual box on hackthebox.eu. Since then I’ve rooted about a dozen others, listened to half of the Darknet Diaries podcast archive, watched hour after hour of DEFCON and Black Hat talks, and read more about both offensive and defensive security than is even remotely reasonable. Drinking from a firehose, as it were.
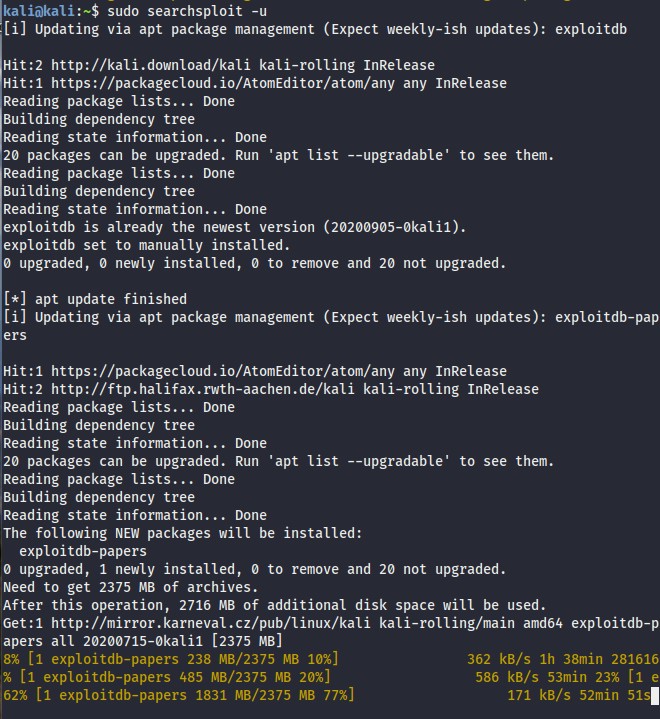
As is my Kali VM
I’m hooked, and therein lies the problem: I’m back to not knowing what I don’t know.
When I began studying computer science I remember dozens of interactions with people asking “What do you want to do in tech?”. I never had an answer to that question because I didn’t have enough knowledge on the various disciplines within CS to form an interest in one. When I decided to pursue CS I didn’t know a database from a server, let alone if there was anything about machine learning which I might find engaging. I spent years feeling like I was fighting my way up the CS mountain, where I’d have an expansive view and understanding of each and every major discipline.

So many options…
That day will obviously never arrive. There are too many niches, nooks, and crannies in the world of technology to ever truly understand (even on an inch-deep basis) what’s happening in every corner of the industry. That is to say nothing of the rate at which it advances.
Information security ultimately appears to be the area where I find the most enjoyment. It’s got a mixture of danger, intrigue, and urgency which I can’t bring myself to ignore. It also has my favorite part of programming: it’s a puzzle.
Which ports are open? Which is running outdated software? What patches haven’t been installed? Who is administering the system and how good are their passwords? Which tools can I use to capture the correct data, which can then be used to exploit vulnerabilities?
How do I filter the noise from the signal and solve this puzzle?
That brings me to my next problem: How do I decide which avenue of security is right for me? Looking at pen-testing tutorials online suggests there is a veritable army of competition for vanishingly few actual positions, though there appears to be a massive drop-off in interest beyond introductory tutorials. Entry level analyst positions are not particularly easy to find at the moment, and those that exist require costly certifications (a few of which I could likely pass with what I learned at UW were it not for the fees). Research positions, where my CS background would likely be an advantage, are also mostly looking for far more experience than I have.
I don’t really know how to proceed here. All I’m certain of is that the more I read, watch, listen to, and practice, the better I am as a candidate for any of these positions. I’m never going to know every little thing about this subset of the technology industry, either, but damned if that’s going to stop me from trying.