Challenge 1:
Name: DOM XSS + Bonus Payload
Description: Perform a DOM XSS attack with <iframe src=”javascript:alert(`xss`)”>.
Difficulty: 1 star
Category: XSS
Expanded Description: https://pwning.owasp-juice.shop/part2/xss.html
Challenge 2:
Name: Bonus Payload
Description: Use the bonus payload in the DOM XSS challenge.
Difficulty: 1 star
Category: XSS
Expanded Description: https://pwning.owasp-juice.shop/part2/xss.html
Tools used:
None.
Resources used:
None.
Methodology:
The only two things necessary for a successful DOM XSS attack are a payload and an improperly sanitized user input field. Fortunately, the payload is supplied, so we don’t need to get particularly fancy. Probing for XSS vulnerabilities with this payload, which is intended to instantiate a pop-up box with “xss” written inside of it, is about as routine as can be.
When opening the homepage, the first place to try is going to be the search feature, so go ahead and give it a shot! Just copy/paste the payload into the search field and hit enter.
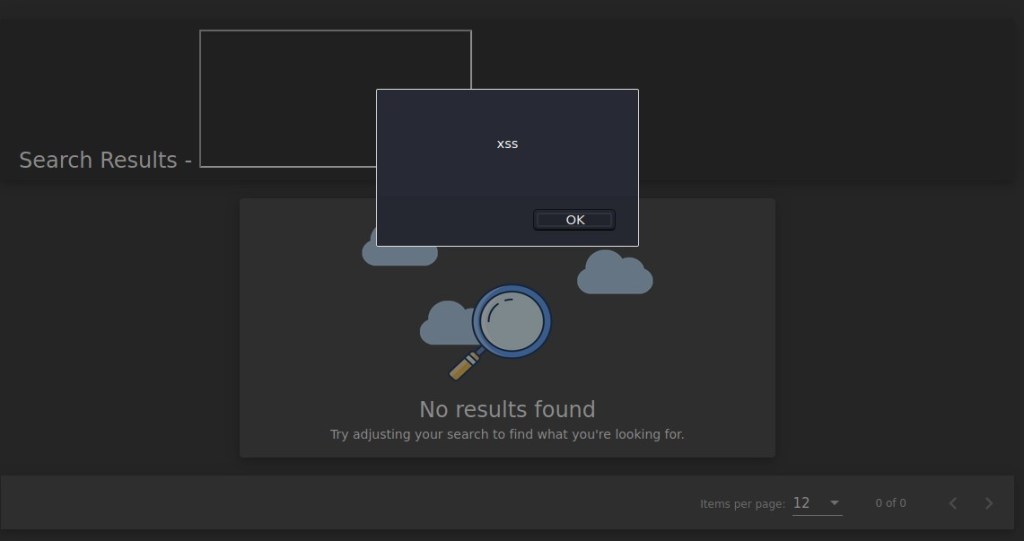

Huzzah! Now that we’ve found a vulnerability with this field, it’s the perfect opportunity to cross another challenge off of our list. Collect the payload from the “Bonus Payload” challenge and enjoy your folksy reward!

Prevention and mitigation strategies:
Input. Sanitization. There’s no legitimate reason for ‘<‘ to exist anywhere in that form. Don’t just sanitize the first n indices, either. It works just as well at index 300 as it does at index 0.
Lessons Learned and Things Worth Mentioning:
- Infosec music exists. Honestly, it isn’t half bad, and there’s more on the Soundcloud page. I’ve been listening to it for an embarrassing length of time as I write this.
- The DOM XSS challenge payload is remarkably useful. It’s now been added to my quick reference notes for future use