Challenge 1:
Name: Meta Geo Stalking
Description: Determine the answer to John’s security question by looking at an upload of him to the Photo Wall and use it to reset his password via the Forgot Password mechanism.
Difficulty: 2 star
Category: Sensitive Data Exposure
Expanded Description: https://pwning.owasp-juice.shop/part2/sensitive-data-exposure.html
Challenge 2:
Name: Weird Crypto
Description: Inform the shop about an algorithm or library it should definitely not use the way it does.
Difficulty: 2 star
Category: Cryptographic Issues
Expanded Description: https://pwning.owasp-juice.shop/part2/cryptographic-issues.html
Tools used:
Burp, FoxyProxy, ExifTool
Resources used:
CrackStation Password Hash Cracker
Methodology:
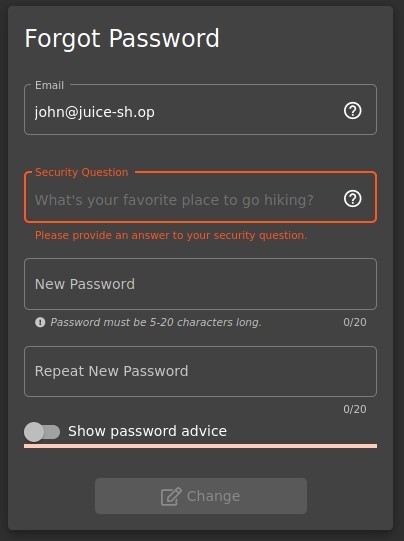
Before going to the photo wall, it’s important to know what we’re looking for, so open the “Forgot Password” link and enter John’s email address (which we collected in the “Admin Section” challenge. Alternatively, guess his email address).
Hiking, eh? OK. Let’s check the Photo Wall. There’s only one photo of a trail, but to be safe it’s a good idea to check the caption: “I love going hiking here… (© j0hNny)”. This certainly appears to be the right photo, so save it to your system and let’s check out the metadata. ExifTool is a fantastic tool for this type of thing.


Fortunately Johnny isn’t savvy enough to strip exif data from his photos, so after looking up how Google Maps wants coordinates to be formatted, format the string and search.
*For a complicated set of reasons, other recommended formats may place the location in an entirely different area, so use “36°57’31.38″ N 84°20’53.58″ W”
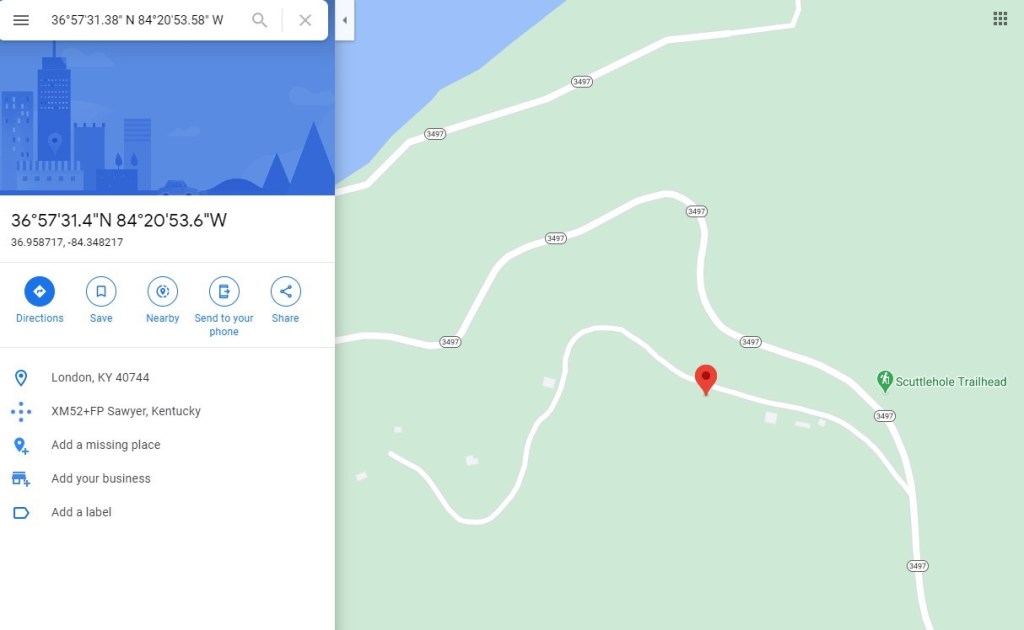
Be aware that you’re not just looking for candidate locations simply in the immediate area, so be sure to zoom out and gather more information about the general area.
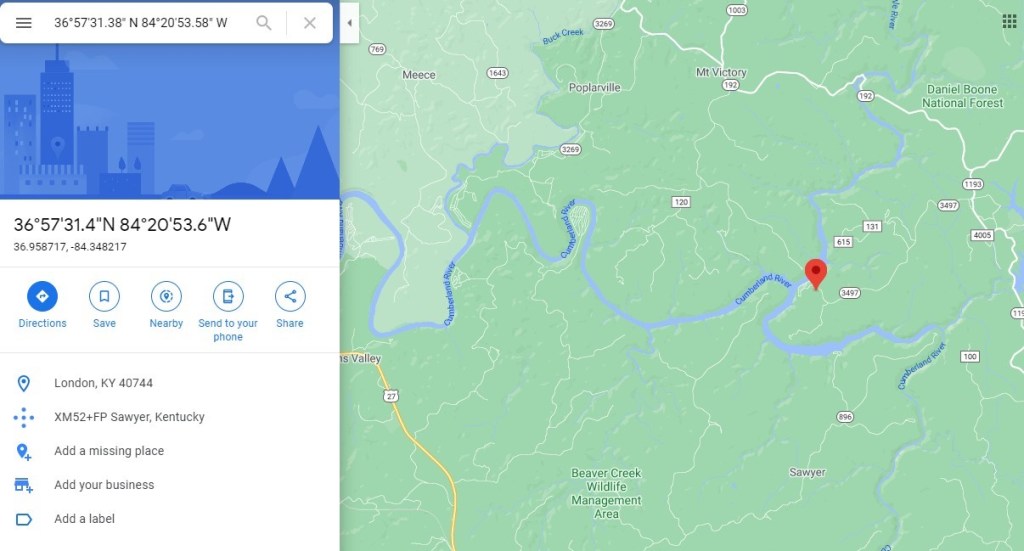
Now that we have enough information to build a list of potential locations, go ahead and do that.
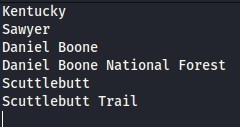
At this point, the obvious tool to use would be Burp’s Intruder, but for the sake of variety I’m going to use Repeater.

After only a few failed attempts, the correct answer returns an abundance of user information.
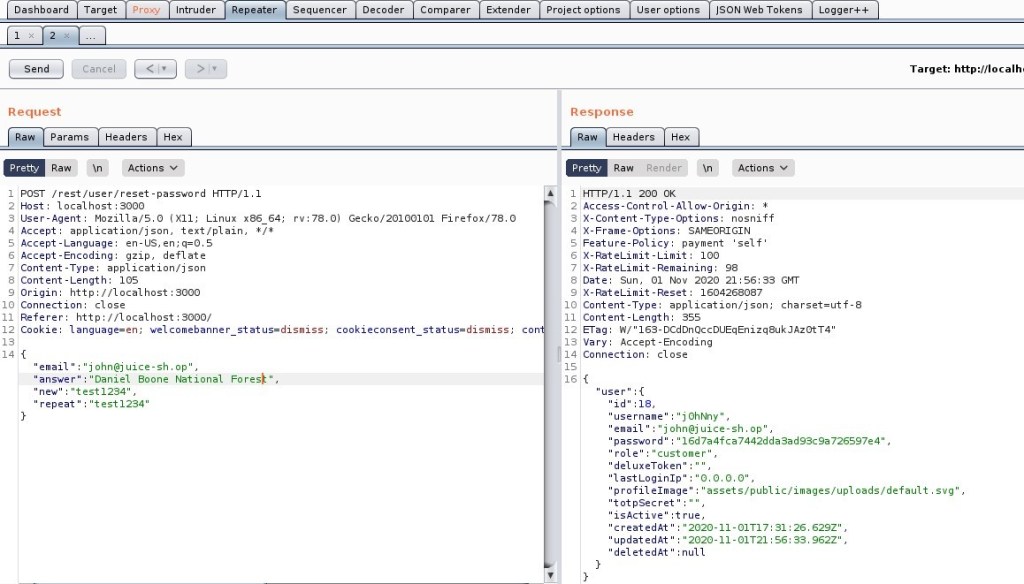
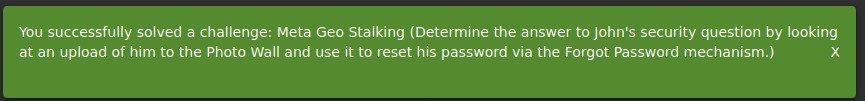
At this point, the Meta Geo Stalking challenge is complete. There is, however, one piece of very useful information in the response packet: the password hash. It would be the height of foolishness to neglect that hash, as there are tools available to analyze it and tell you what hashing algorithm is in use.
Unsalted MD4 and MD5 hashes are barely speedbumps to cracking passwords at this point in time, and should never be used. But we still have two options (MD4 or MD5), and I’d like to know if the server is responding with John’s new password or his old one, so to save time and effort we can use an online password hash cracker. While hashcat and JohnTheRipper are useful tools, they are more labor intensive than is necessary for one hash. Work smarter, not harder.

With such an outdated encryption algorithm in use, now is a good time to inform the shop of their vulnerability and pass the “Weird Crypto” challenge by submitting a customer feedback form containing the algorithm’s name.

Prevention and mitigation strategies:
OWASP Mitigation Cheat Sheet – Meta Geo Stalking
OWASP Mitigation Cheat Sheet – Weird Crypto
- Strip EXIF data from your photos before posting them publicly. Most social media companies do this automatically, but it is not safe to assume that every site follows that best practice. If you’re working on a website which interacts with user media, strip unnecessary information from it before placing it somewhere your users can access it.
- Use modern, up-to-date hashing algorithms. Passwords stored as md5 hashes are responsible for some of the biggest hacks in the last decade.
Lessons Learned and Things Worth Mentioning:
- Kali, while tremendously capable, is not an all-in-one package. When running into situations where I want to solve a specific problem and Kali doesn’t have a relevant tool, I always try to track one down. ExifTool is a perfect example of this in action. It’s nice when that effort pays off in subsequent situations.