Challenge:
Name: View Basket
Description: View another user’s shopping basket.
Difficulty: 2 star
Category: Broken Access Control
Expanded Description: https://pwning.owasp-juice.shop/part2/broken-access-control.html
Tools used:
Burp Suite, FoxyProxy
Resources used:
None.
Methodology:
The access controls on this site have proven to be fairly poor, so this shouldn’t be terribly difficult. First, we need to see what information is being sent to the server when we click the “View Basket” link, so log in and fire up Burp and set up FoxyProxy accordingly. Then we click on the basket and wait for a JSON object.
Except it never comes. Curious, that. Let’s look at the destinations for these packets. If it’s not a JSON object being sent, then maybe our user information is being passed to a unique link.
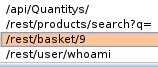
Hmm. I wonder if that ‘9’ (or whatever number is there for you) is an identifier. We know from the Admin Section challenge that there are more than nine users, but let’s set it up to make sure we’re actually viewing another user’s basket.
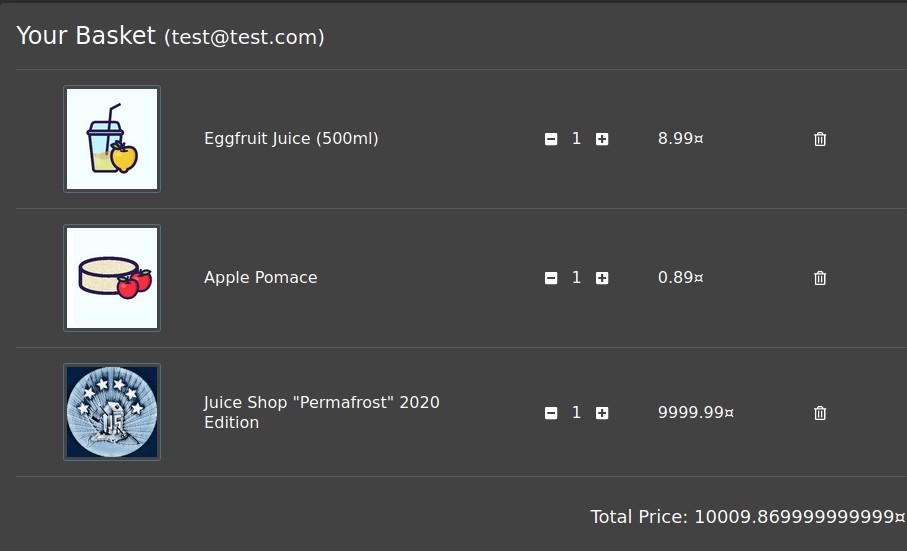
First, let’s add a few specific items to our own basket so we can identify it if we can successfully view basket 9 from another account. Then either create another account or log into another one you’ve got access to (any of the Login, Password Reset, or Geo Stalking challenges should have left you with persistent access to those accounts) and go to that user’s shopping basket. Now all that’s needed is to send that user’s initial request packet to Burp’s Repeater, change the number next to “basket/” to whatever number your user had, and send it off.


Prevention and mitigation strategies:
User 10 should never be able to access user 9’s basket. User 9’s cookie information should reflect their identity, so use that user’s cookie to authenticate and allow access to their private information. Anyone not in possession of that cookie should receive a 403 response code.
Lessons Learned and Things Worth Mentioning:
It’s been a while since I initially solved this, and had become dependent upon JSON data for my attacks. That probably didn’t cost me more than 30 seconds of confusion, but hopefully after this that delay will be significantly reduced.