Challenge:
Name: Steganography
Description: Rat out a notorious character hiding in plain sight in the shop. (Mention the exact name of the character)
Difficulty: 4 star
Category: Security Through Obscurity
Expanded Description: https://pwning.owasp-juice.shop/part2/security-through-obscurity.html
Tools used:
OpenStego, StegHide, exiftool
Resources used:
None.
Methodology:
Steganography both fascinates and confuses me. The idea of hiding data in plain sight with only a trivial chance of it being detected is something I like for some reason. That it’s not just limited to photos, but also video and audio is just icing on the cake. I remember distinctly solving the “Milkshake” stego challenge on hackthebox.eu and being dumbfounded at how borderline-impossible that would be for a casual audiophile to discover. Naturally, then, this was a challenge I had been looking forward to for a while. I even had an idea of where to start.
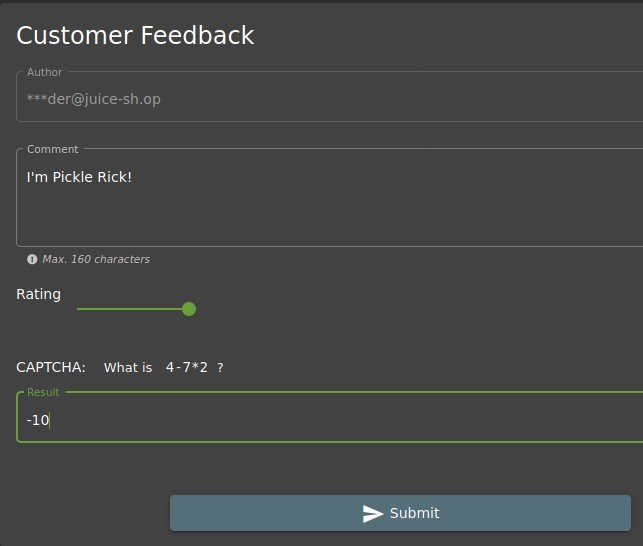
This review, “Nothing useful available here!”, has always bugged me. Assuming this was related to this specific challenge, I opted to download all of these images and dig through them. As they can’t be save directly, you must inspect the page, find the image file locations, and download them manually.
![- GIMP
File
[I] (imported)-2.O (RG B color 8-bit gamma integer, G I M P bu ilt-in sRG B, I layer) 400x300
Edit Select View Image Layer Colors Tools Filters Windows Help
1.
2. Hardness 050 (51 51)
Basic,
Current layer only
Delete cropped pixels
Allmv g rcwing
Expand from center
Fixed Aspect ratio v
400:300 a D
Position:
Mode
10.0
Normal v
100.0
v
100%
v l.jpg (1.1 MB)](https://curiositykillscolby.com/wp-content/uploads/2020/12/image-27.jpeg?w=916)
Looking through the files with GIMP, nothing really jumped out at me. I tried StegoHide as well, but without a passphrase there was no way to extract potentially hidden data from any of the files. One thing jumped out at me, though. All but one of the image files was in .jpg format, with one outlier in .png.
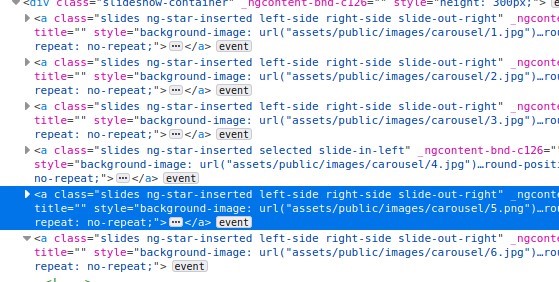
Since I knew that StegoHide wasn’t the right tool, I opened OpenStego and attempted to find hidden data in the .png file.

Success! Here’s the image hidden in the PNG file:

Now just submit the Customer Feedback form with the character’s name in the Comment section and you’re done!