Challenge:
Name: Expired Coupon
Description: Successfully redeem an expired campaign coupon code.
Difficulty: 4 star
Category: Improper Input Validation
Expanded Description: https://pwning.owasp-juice.shop/part2/improper-input-validation.html
Tools used:
Burp Suite, FoxyProxy
Resources used:
Methodology:
The expanded description notes two important items: there are clues concerning a past campaign in the application itself, and also that time travel is not actually necessary. That’s kind of a curious thing to throw in, but like many other things on this application I chalked it up to this being a fun-loving project.
Anyhow, let’s start by finding the discount code in the main-es18.js file.
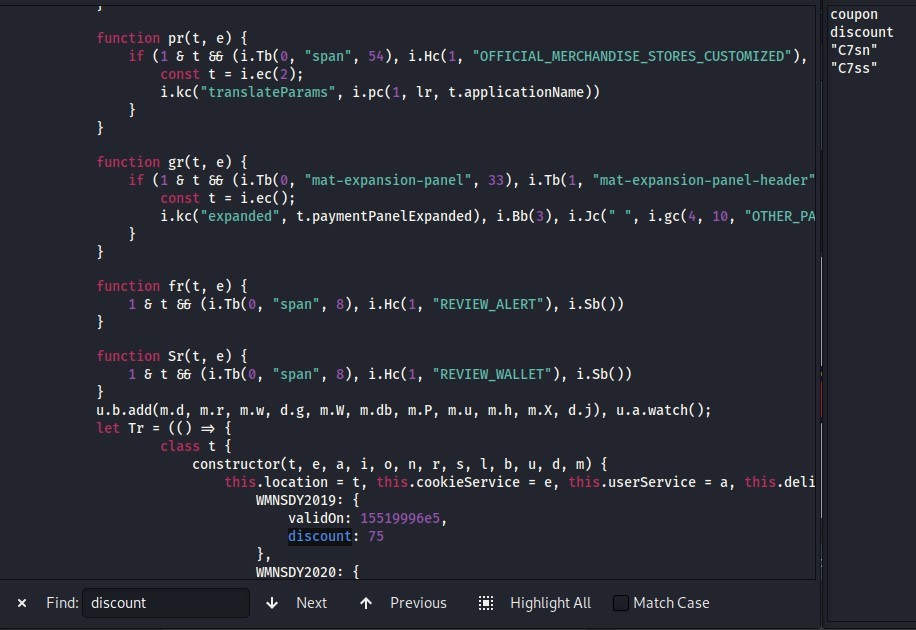
It looks like we have Women’s Day coupon codes listed out for us. Let’s give the 2020 one a shot.
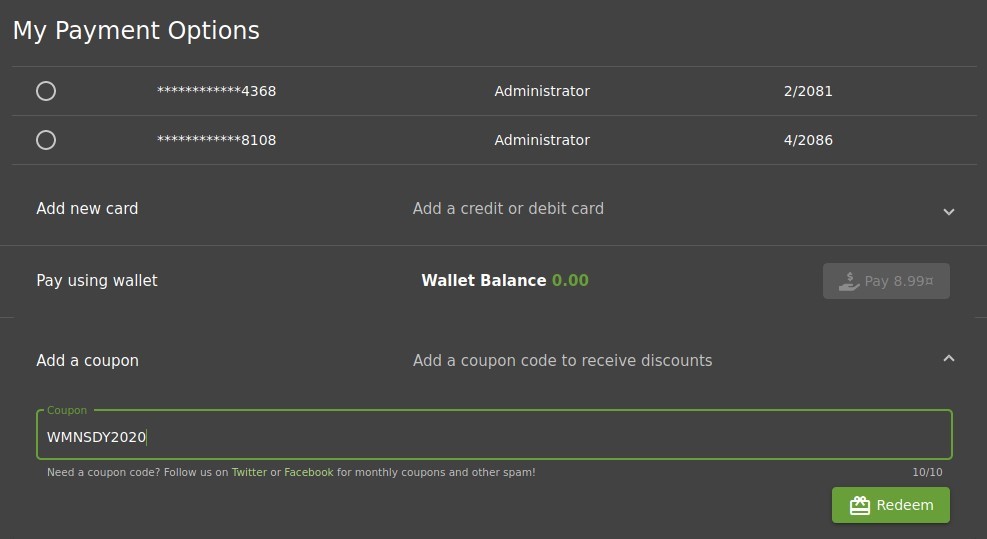
No dice.
If the coupon code’s acceptance criteria is time-bound, then the only way for this challenge to be possible is for the time and date calculations to be completed on the client side. Were they authenticated by the server, then time travel might actually be necessary. In that case, it’s time to do some research on past Women’s Days.
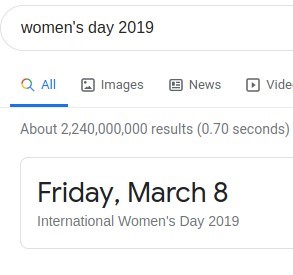
With March 8, 2019 as our target date, it’s time to update our operating system’s date using timedatectl’s set-time function.

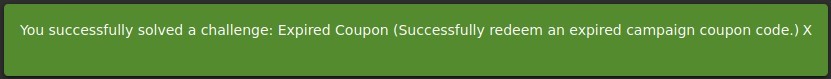
Now, just copy/paste the coupon code from Women’s Day 2019 into the coupon redemption field and click “Redeem”.
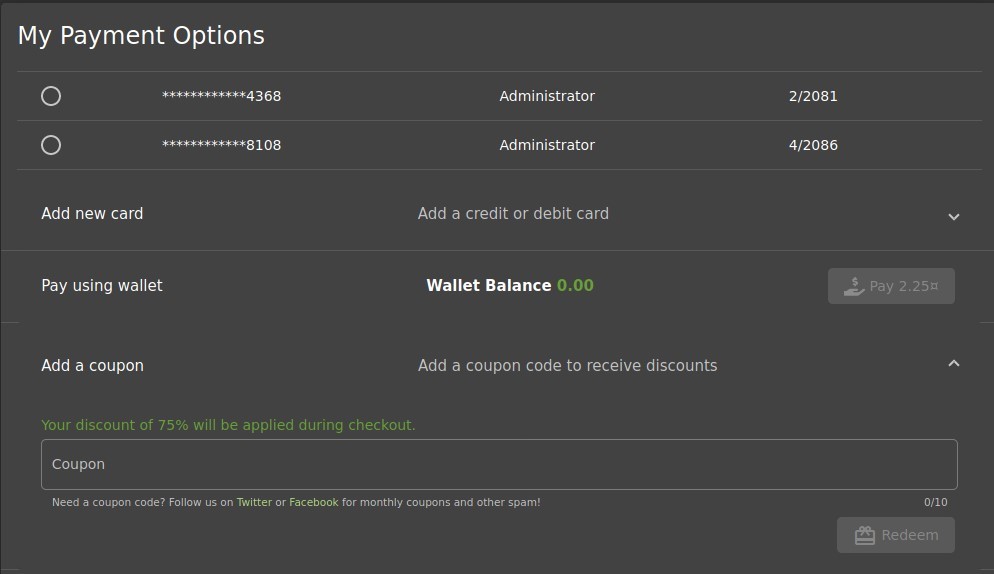
**Don’t forget to reset your operating system’s date once you’re done.**
Prevention and Mitigation Strategies:
Server-side authentication of coupon codes would have rendered this attack vector useless. Client-side authentication works for certain things, but over and over in this application it has proven to be insufficient to prevent abuse.
Lessons Learned and Things Worth Mentioning:
I knew on some level that updating my system’s date was possible, as I remember doing it on my Macintosh Performa 550 back in 1999 to see if my computer would spontaneously combust because of Y2K (yes, I’m old), but it never occurred to me that the authentication for coupon codes would be done on the client side. Having seen the URL endpoint for coupon codes using Burp Suite, I incorrectly assumed that the server was authenticating the code. I should have paid closer attention to when the packet was sent versus when the redemption success/failure appeared on my browser.