Challenge:
Name: Access Log
Description: Gain access to any access log file of the server
Difficulty: 4 star
Category: Sensitive Data Exposure
Expanded Description: https://pwning.owasp-juice.shop/part2/sensitive-data-exposure.html
Tools used:
Dirbuster
Resources used:
PREREQUISITE: LOGIN SUPPORT TEAM
Methodology:
**In order to complete this challenge, you must be logged in as support@juice-sh.op. A link to that challenge walkthrough is located above.**
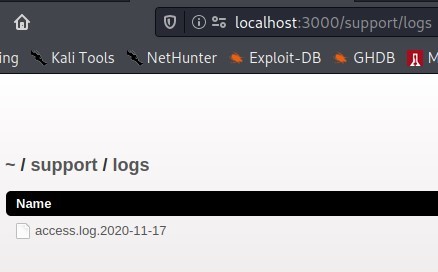
In the expanded description, it’s heavily suggested that only the support team has access to wherever this file is located. After logging in as support@juice-sh.op, a recursive brute-force directory search using Dirbuster, Gobuster, or any other directory enumerating tool will reveal that there is a directory named “/support/logs”. Simply go to that address and download the access log.

Prevention and Mitigation Strategies:
Lessons Learned and Things Worth Mentioning:
- Making the location accessible only to the support team is smart. I had run Dirbuster and Gobuster on this several times (with varying levels of success and rates of error codes), but without being able to access the support directory I could never have known for sure that the logs were contained within.
- User-dependent access is something I’ll need to keep in mind as I move into the more difficult challenges. I can’t imagine that this is the only time this particular trick will be used in this application.