Challenge:
Name: Legacy Typosquatting
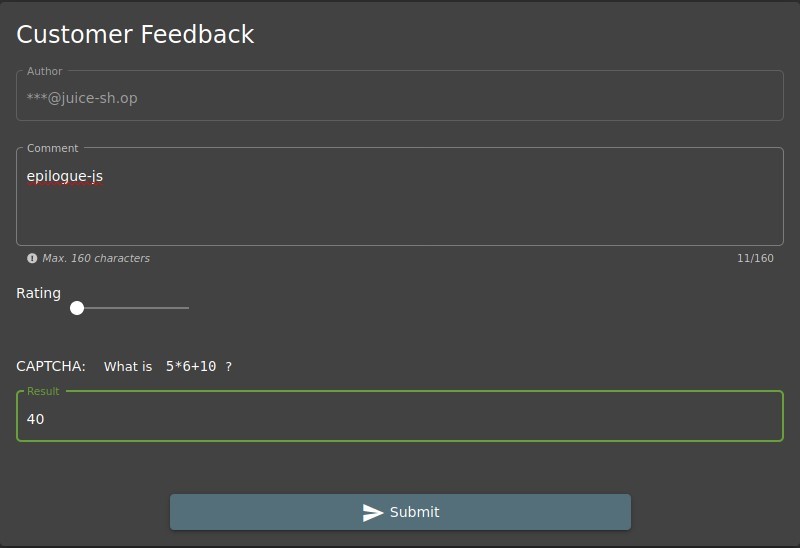
Description: Inform the shop about a typosquatting trick it has been a victim of at least in v6.2.0-SNAPSHOT. (Mention the exact name of the culprit)
Difficulty: 4 star
Category: Vulnerable Components
Expanded Description: https://pwning.owasp-juice.shop/part2/vulnerable-components.html
Tools used:
None.
Resources used:
Poison Null Byte / Developer Backup
Methodology:
While the expanded description points you to a blog post about malicious packages, and that blog post lists vulnerable libraries to search for this error, I actually “solved” this long ago.
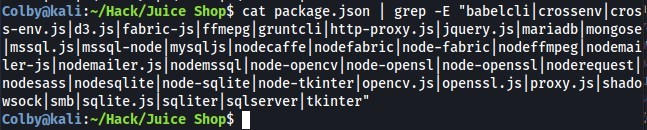
The way I solved this challenge was by being thorough in the Vulnerable Library challenge, and taking a screen shot of the snyk.io description of the “epilogue-js” library found in the Developer Backup challenge.

Prevention and Mitigation Strategies:
OWASP Vulnerability Dependence Management Cheat Sheet
Lessons Learned and Things Worth Mentioning:
Proper Prior Planning Prevented Colby from having to tackle this challenge from scratch. Always gather every piece of information available to you in order to gain a potential advantage down the road.