Challenge:
Name: Login Bjoern
Description: Log in with Bjoern’s Gmail account without previously changing his password, applying SQL Injection, or hacking his Google account.
Difficulty: 4 star
Category: Broken Authentication
Expanded Description: https://pwning.owasp-juice.shop/part2/broken-authentication.html
Tools used:
Burp Suite
Resources used:
https://mothereff.in/reverse-string
Methodology:
This was a fun, CTF-type challenge. The expanded description talks about Oauth at length, so I began by looking for any reference to it in the main javascript file.
![Shop$ cat main.js I grep "oauth"
Login(t) {
oauth
return this.http.get( "https•.//wm.googleapis.com/
oauth
this. userservice. oauth
oauth:
["app
-oauth"
this.configurationservice = t, this.usersewice = e, this.windowRefSewice = a, this.cookiesewice = i, this.r
[c.y.required]), this .passwordControl = new c.
outer = o, this.formsubmitsewice = n, this.ngzone = r, this .emailcontrol = new c.d("",
[c.y.required]), this.hide = this.rememberMe = new c.d( !1), this.clientld = "
d("",
1005568560502-6hm161ef80h46hr2d98vf20h1nj4nfhq.
apps.googleusercontent.com", this.
oauthUnavailable = !ø, this.redirectUri =
e ? (this.oauthUnavailable = !1, this.redirectUri = e.proxy ? e.proxy : e.uri)
: (this.oauthUnavailabl
e = !ø, console.log(this.redirectUri + " is not an authorized redirect URI for this application.
this. wi ndowRefSewice. nati vewindow. location. replace( https ://accounts.google.com/o/
oauth
this. clientld . redirectUri} )
i.Tb(23, "mat-icon"), i.Hc(24, "
exit_to_app "), i.sb(), i.Hc(25), i.fc(26,
"translate"), i.sb(), i.Tb(27
15), i.Hc(28), i.fc(29,
17), i.Tb(
, "mat-checkbox" ,
"translate"), i.Sb(), i.Fc(30, fa, 7, ø, "div", 16), i.Fc(31, sa, 4, 3,
"button"
18), i.Tb(33, "a", 19), i.Hc(34, "NO_CUSTOMER"), i.Sb(), i.Sb(), i.Sb(), i.Sb(), i.Sb()), 28 t 88 (i.Bb(4), e
"div",
32,
.error), i.Bb(5), e.emailcontrol), i.Bb(2), i.kc("nglf", e.emailcontrol.invalid), i.Bb(4), e.p
e.hide ? "password" : "text"), i.Bb(2), i.kc("nglf",
e.hide), i.Bb(1), i.kc("nglf", !e.hide), i.Bb(1), i.kc("n
asswordControl "type" ,
e.passwordcontrol.invalid), i.Bb(3), !e.emailcontrol .value
!e.passwordControl .value), i.Bb(3), i.Jc("
i.g
gif" ,
"BTN_LOGIN ), " "
" ) , i. Bb(2), i. "formControl " ,
e.rememberMe), i.Bb(1), i.Jc(" "
, i.gc(29, 16, "REMEMBER_ME ) " "
), i.Bb(2
c(26, 14,
), i.kc("nglf", 'e
Unavailable), i.Bb(1), i.kc( "nglf", !e.oauthUnavailable))
. oauth
Colbyakali :-/Hack/Juice Shop$](https://curiositykillscolby.com/wp-content/uploads/2020/12/image-90.jpeg?w=1024)
Ok, there are enough references there to warrant a deeper look, so I dug into the code until I came across the login function.
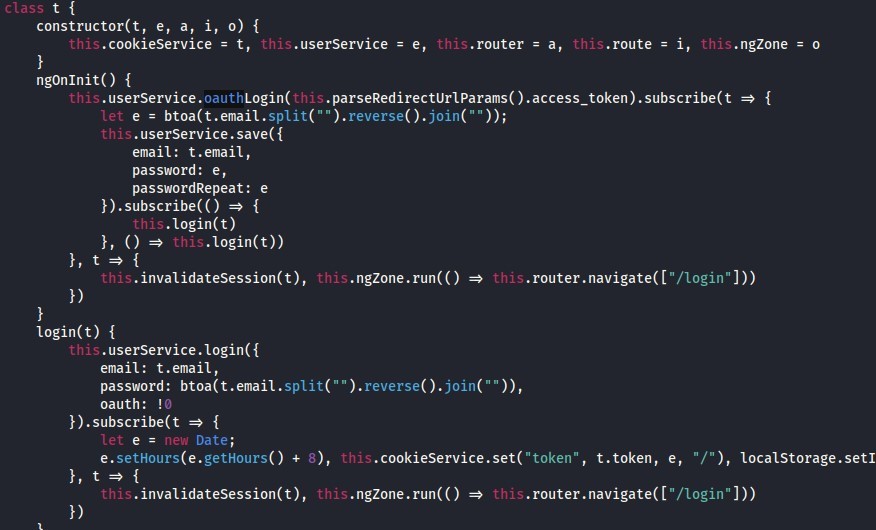
While other code obfuscation in this file consists of one or two letters, “btoa” didn’t quite fit that mold, so I googled it.

If btoa() is just a base64 encoding function, and it is just encoding a reversed string consisting of the user’s email address, then let’s go ahead and do just that.


![Dashboard Target
Intruder Repeater
Sequencer
Decoder
HIT P history WebSockets history Options
Request to http://localhost:3000
[127 001]
Para ms Headers
Comparer
Open Browser
Raw An
Pretty
•Actions
POST /rest/user/login HTTP/I.I
Host: local host 3000
User-Agent: MoziIIa/S.O (X
11; Linux x86 64;
application/ j son, text/ plain,
Accept
Accept -Language: en-lJS, en; q=O.S
Accept -Encoding: gzip, deflate
Content -Type: application/ j son
Content -Length: 88
Origin: http•
// I Ocal host 3000
Connection: close
Referer: http
// I Ocal host 3000/
rv.78.o)
Gecko,'20100101 Firefox,'7;
Cookle: language=en; welcomebanner status=dismiss;
email
'bjoern.kimminich@gmail . com",
passwo rd' " bR9j LmxpYWInQGhj aRSpbRIpaySucmVvamIK
cookleconsent
status=dismi:](https://curiositykillscolby.com/wp-content/uploads/2020/12/image-89.jpeg?w=560)
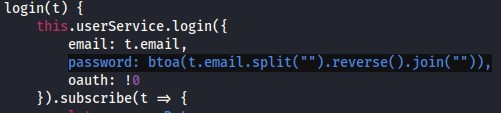
But it didn’t work. After all that sleuthing, the password didn’t work. I double and triple checked every character in the email address, made sure the reversing method was functioning properly, and finally tried to encode the string using Burp Suite’s Decoder.

What’s this? A different character at the end of the encoded string? Let’s give it a shot!

Prevention and Mitigation Strategies: