Challenge:
Name: Admin Section
Description: Access the administration section of the store.
Difficulty: 2 star
Category: Broken Access Control
Expanded Description: https://pwning.owasp-juice.shop/part2/broken-access-control.html
Tools used:
Python’s json.tool module, Firefox Developer Tools, MousePad
Resources used:
None.
Prerequisite challenges for this methodology:
Methodology:
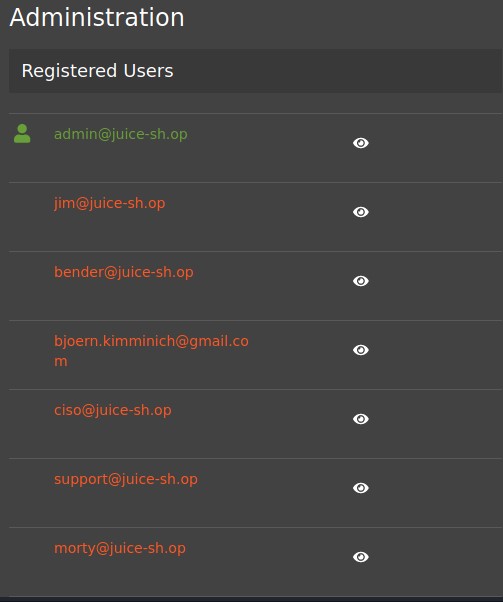
As the expanded description states that this is an easily guessable url, I logged in as admin@juice-sh.op did just that and found it on the first try: http://localhost:3000/administration. Kind of anticlimactic as challenges go, but this is where the keys to the kingdom are held, so it’s a good idea to poke around and see what you can find.
The first thing that jumped out at me was that this page listed all of the registered users. That data had to get to my system somehow, and since it showed that I was logged in it had to contain more than just one piece of data about the users.
To see how much more I could find I decided to use Inspect Element to see what other user data I could find. While the HTML may not contain anything juicy (Get it? Get it?), the networking tab on this site almost certainly would.
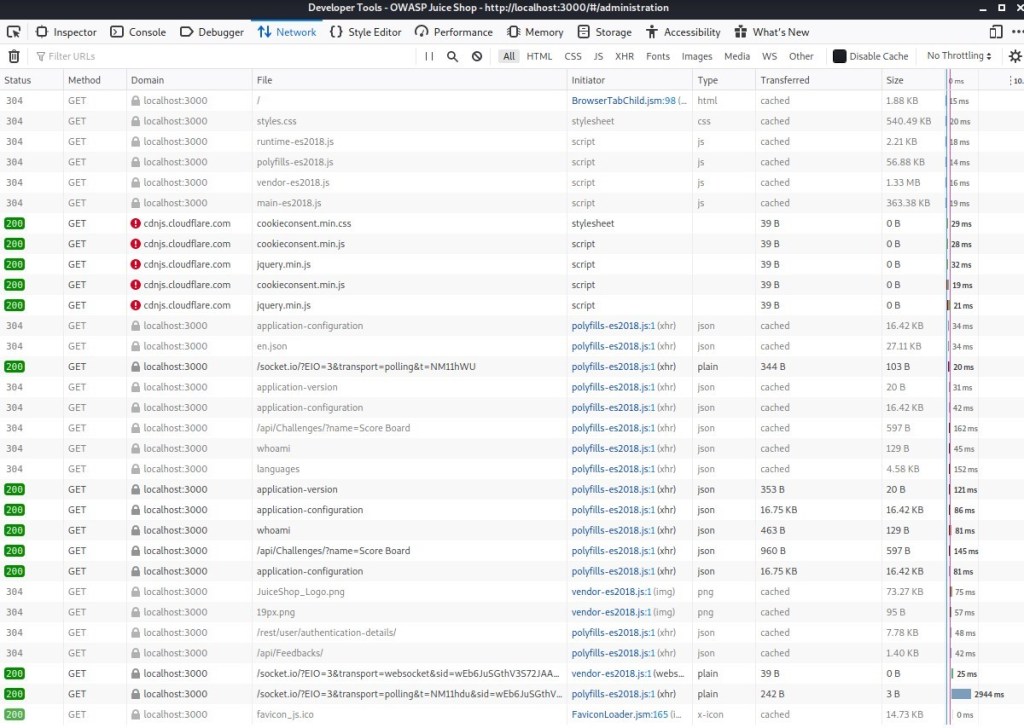
Immediately I noticed “/rest/user/authentication-details/”, so I opened it up to take a look. Lo and behold, a JSON file with loads of user data! I quickly copy/pasted to a MousePad file, formatted it using Python’s json.tool module, and saved it for future use.
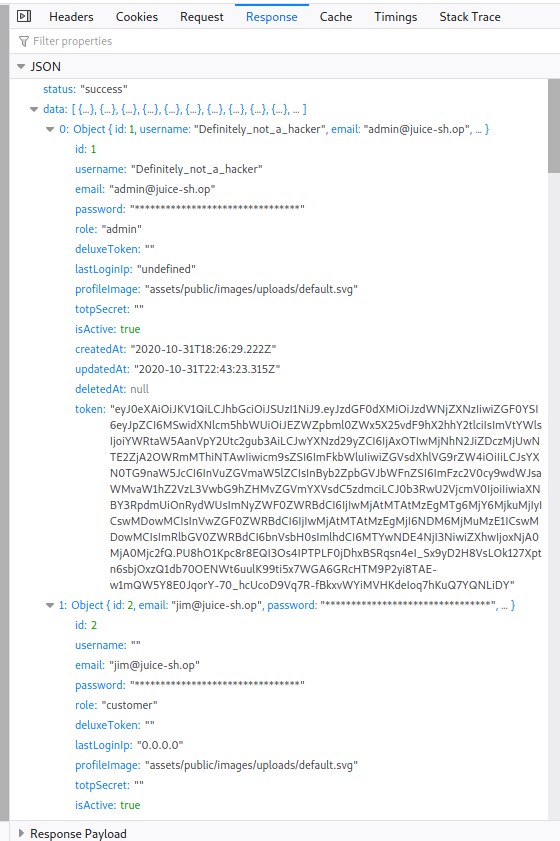
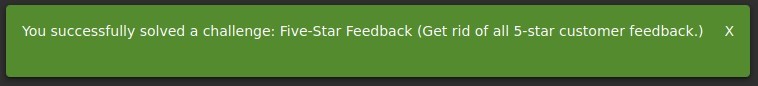
Next I saw “/api/feedback/” tab, so I did the same thing there. I wanted to have as much information as I could possibly get my hands on, because by knowing the format of these JSON objects I could use that formatting data to complete other challenges. I knew that there were challenges related to this file (deleting all of the 5 star reviews, leaving a 0 star review, leaving a review in another user’s name, etc) and this file would certainly make them easier to complete.
After doing the same one more time for the “application-configuration” response, I was satisfied that, at least as far as the things I knew to look for, I had captured the information I was after. The JavaScript scripts are definitely worth grabbing as well, but I already had those.
Prevention and mitigation strategies:
While I couldn’t log into the administration page with a non-admin user, that’s a fairly substantial single point of failure considering the amount of information available on this page. Even though the page itself is not linked to from anywhere else on the site, having such an easy to guess link isn’t a great idea. I’d suggest obfuscating it by changing the url to something much more secure. Heck, you could go nuts and use something like a base 64 encoded password just to find the page. Furthermore, enabling multi-factor authentication and using a very restrictive whitelist would offer additional protection
Lessons Learned:
- The companion guide isn’t joking about “easily guessable”.
- There is a deep well of information on an administration page which can be used to craft much more sophisticated attacks on a site’s vulnerabilities. Knowing where the weaknesses are located is of tremendous value.
- “python -m json.tool [filename.json] > [output.json]” is a fantastic tool for formatting JSON files. That command is now included in my quick reference notes file.