Challenge:
Name: Password Strength
Description: Log in with the administrator’s user credentials without previously changing them or applying SQL Injection.
Difficulty: 2 star
Category: Broken Authentication
Expanded Description: https://pwning.owasp-juice.shop/part2/broken-authentication.html
Tools used:
Burp, FoxyProxy
Resources used:
None
Methodology:
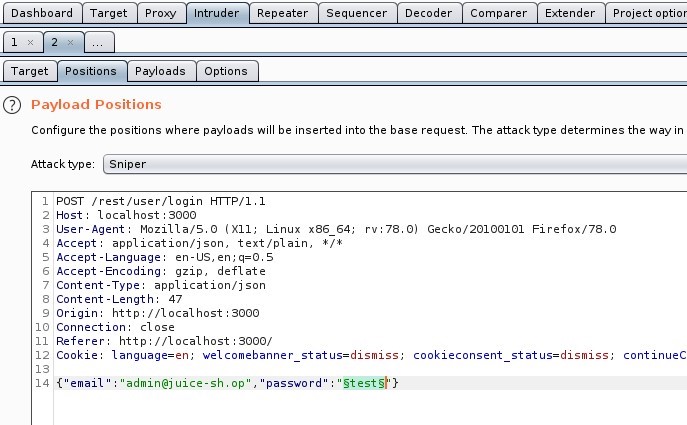
If we’re trying to guess the admin’s password without any SQL trickery, then Burp’s Intruder Sniper attack is the first thing that pops into my head. Set up Burp and FoxyProxy to capture a login packet, then send that packet to Intruder and set up your Sniper attack.
Now for the complicated part: finding a password list with common passwords, but without resorting to RockYou.txt. The one which made the most sense to me was located in /usr/share/wordlists/fern-wifi. The “common.txt” wordlist there seemed to have a number of potentially easy-to-guess passwords with an emphasis on administrator accounts.
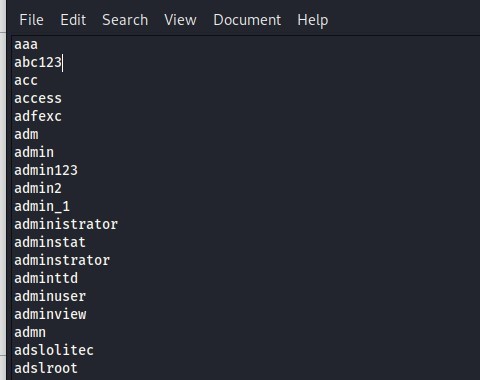
Copy/paste the contents of the wordlist to Intruder’s Payload tab and wait for a 200 status code. Don’t worry, you won’t be waiting long.

Now log in and enjoy your full administrator privileges!
Prevention and mitigation strategies:
Take password security seriously. If you absolutely must share your passwords with someone else (spouse, shifty stranger, etc), then do not send it SMS, Email, or any other electronic medium without first encrypting the file. Generating and using an RSA key pair is a pain (not to mention getting the other person to do it), but it beats having your identity stolen.
Use unique passwords for every account you have. When I took my first security course a year ago I was one of those people who reused a few passwords over and over. Today I carry a cipher with me everywhere I go (qwertycards.com has credit card-sized unique ciphers for $5), and to keep myself from forgetting any of the dozen different password character restrictions I’ve encountered, I store all of my passwords in a password manager.
Password managers aren’t 100% secure (nothing is), either. But someone has to seriously want your passwords to use tools like KeeFarce, for KeePass2.x, successfully.
Lessons Learned and Things Worth Mentioning:
- Nothing, really. I’ve done this a few dozen times.
- Ideally I’d have used Hydra, but rather than explaining the syntax and what it actually does, this approach was serviceable and led to the desired outcome.