Challenge:
Name: CAPTCHA Bypass
Description: Submit 10 or more customer feedbacks within 10 seconds.
Difficulty: 3 star
Category: Broken Anti-Automation
Expanded Description: https://pwning.owasp-juice.shop/part2/broken-anti-automation.html
Tools used:
Burp, FoxyProxy
Resources used:
None.
Methodology:
As usual, I started with the expanded description, which provided three possible methods for completing this challenge. Only one looked appealing, however.
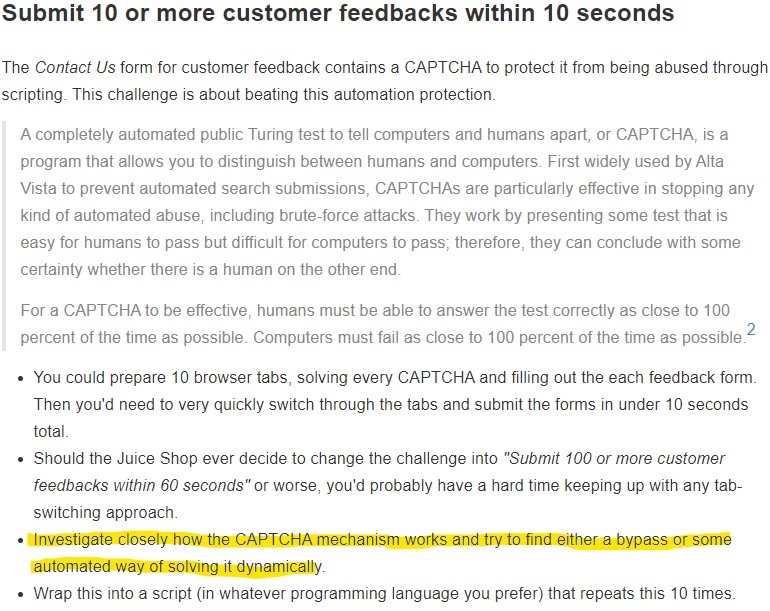
First let’s figure out how the CAPTCHA mechanism works. I set up Burp and FoxyProxy, then made my way to the Customer Feedback form.
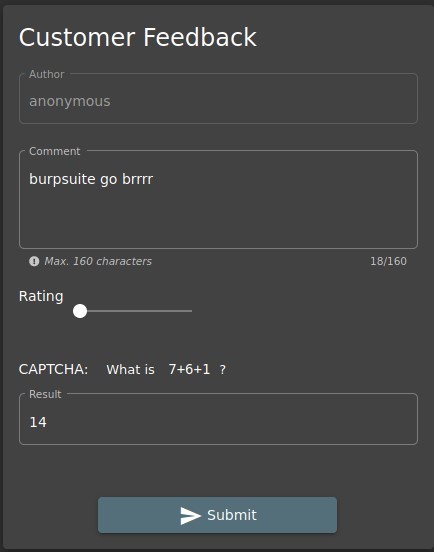
Nothing on the screen jumped out at me, so after filling in the form, I sent it off to Burp for analysis.

If “captchaId” is always 0, and the answer to “captchaId” 0 is always 14, then all that really needs to be done to bypass the CAPTCHA and complete the challenge is to send the packet to Burp’s Repeater tab and spam the “Send” button until you see…

Prevention and Mitigation Strategies:
Use actual CAPTCHA, only allow registered users to submit feedback, and limit the number of feedback comments each registered user is allowed to submit in a given time span.
Lessons Learned and Things Worth Mentioning:
- CAPTCHA is successful for a variety of reasons. Home-brewed CAPTCHA copies are never going to be as sophisticated as the real thing.
- While the other two methods suggested in the expanded description would all work, I chose this method because every bit of practice I can get with Burp Suite helps me get more comfortable with it.