Challenge:
Name: Product Tampering
Description: Change the href of the link within the OWASP SSL Advanced Forensic Tool (O-Saft) product description into https://owasp.slack.com
Difficulty: 3 star
Category: Broken Access Control
Expanded Description: https://pwning.owasp-juice.shop/part2/broken-access-control.html
Tools used:
Burp, FoxyProxy
Resources used:
Methodology:
First, it’s important to read the expanded description in order to acquire the payload you’re supposed to be pushing to the product database.
Payload acquired, it’s time to find out more about the product which is to be modified.
![Table: Products
[41 entries]
I id | 255 |
name
1
3
4
5
6
7
8
10
11
12
255
255
255
255
255
255
255
255
255
255
255
255
Apple Juice (løøøml)
Orange Juice (løøøml)
Eggfruit Juice (5øøml)
Raspberry Juice (løøøml)
Lemon Juice (5øøml)
Banana Juice (løøøml)
OWASP Juice Shop T-Shirt
OWASP Juice Shop CIF Girlie-shirt
OWASP SSL Advanced Forensic Tool (O-saft)
Christmas Super-surprise-Box (2014 Edition)
Rippertuer Special Juice
OWASP Juice Shop sticker (2015/2016 design)
image
apple_juice.jpg
orange_juice. jpg
eggfruit_juice. jpg
raspberry_juice. jpg
lemon_juice. jpg
banana_juice.jpg
fan _ shirt . jpg
fan_girlie. jpg
orange_juice . jpg
undefined. jpg
undefined . jpg
sticker. png
I price
1.99
2 .99
8.99
4.99
2.99
1.99
22 .49
22.49
0.01
29.99
16.99
999.99](https://curiositykillscolby.com/wp-content/uploads/2020/11/image-129.jpeg?w=904)
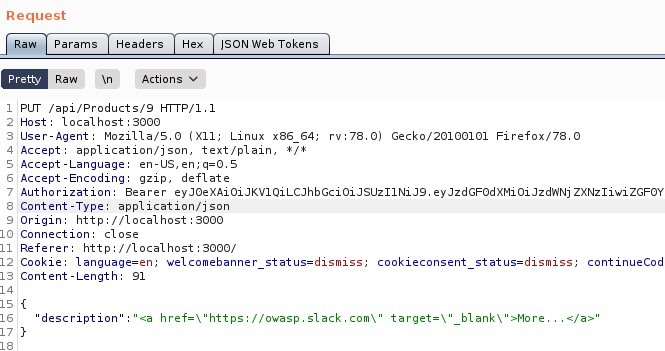
After making note of product ID number, I fired up Burp Suite and set up FoxyProxy to start tinkering with packets. I knew, thanks to the expanded description, that this challenge would require direct modification of the database via the API. That pointed me in the direction of crafting a packet to use the PUT command, to send to that product’s URL. Thanks to all of the database information I collected in the Database Schema challenge, I even knew which field to update and how to accomplish that.
After sending that packet off, this was the response:
![Response
Pretty
Headers
Render
Raw
200 0K
_Actions
Access-Cont rol -Allow-origin: 1
S X-Content -Type-options: nosniff
SAMEORIGIN
Feature-policy: payment
self'
Content -Type: application/ j son; charset=utf-
7 Content -Length:
a-rag: W,' 13f-yshi4Rv1F6GbDS+0Ü,NqVt9DrsJM'
Vary: Accept -Encoding
10 Date: Thu, OS Nov 2020 GI•TT
Il Connection:
status
'data"
'name
cl ose
success ,
' O,NASP ssL
'description
price" : 0.01,
'deluxeprice" : 0.01,
" Image
'orange ] ulce.]pg",
Advanced Forensic Tool (O-Saft)
href=\
"http://kimminich.de\
target=
blank \
*ore.
createdAt "
'updatedAt "
'deletedAt'
2020-11-OST17: 21 912Z" ,
'2020-11-OST19: 45: 13. 817?' ,
:null](https://curiositykillscolby.com/wp-content/uploads/2020/11/image-131.jpeg?w=612)

Prevention and Mitigation Strategies:
OWASP REST Security Cheat Sheet
Lessons Learned and Things Worth Mentioning:
PUT commands are something I’ve only used a couple of times before, so I could certainly use more practice with it. Fortunately what I already knew was sufficient for this challenge.