Challenge:
Name: Vulnerable Library
Description: Inform the shop about a vulnerable library it is using. (Mention the exact library name and version in your comment)
Difficulty: 4 star
Category: Vulnerable Components
Expanded Description: https://pwning.owasp-juice.shop/part2/vulnerable-components.html
Tools used:
None.
Resources used:
Poison Null Byte && Developer Backup
Methodology:
In the expanded description of this challenge, we are instructed to use the “Contact Us” form to inform the shop about a vulnerable library it is using. It is also recommended that we look for “… possible dependencies related to security in the package.json.bak you probably harvested earlier during the Access a developer’s forgotten backup file challenge.”
That’s easy enough. Let’s see how many dependencies we’re dealing with.

While this next step might take more time than you want to spend, as always it’s best to gather as much information as you possibly can. That means iterating through this entire list and checking each library using snyk.io to find which libraries and/or versions have (gigantic) security issues.
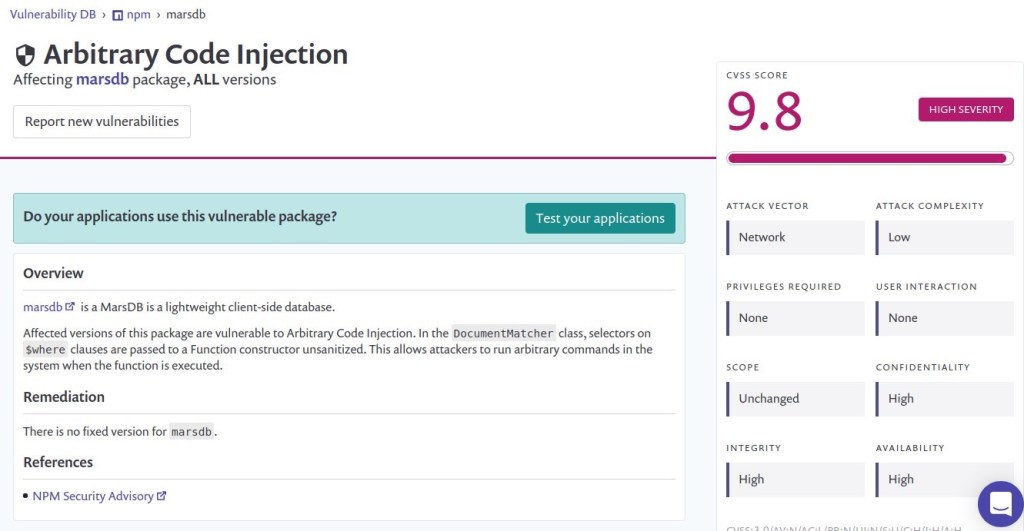
Taking note of the CVSS score for each package, look for something with a score of 8+ (like this marsdb library). CVSS scores are intended to give a quick and dirty (1-10) idea of the severity of the issue, and 9.8 definitely qualifies as severe.
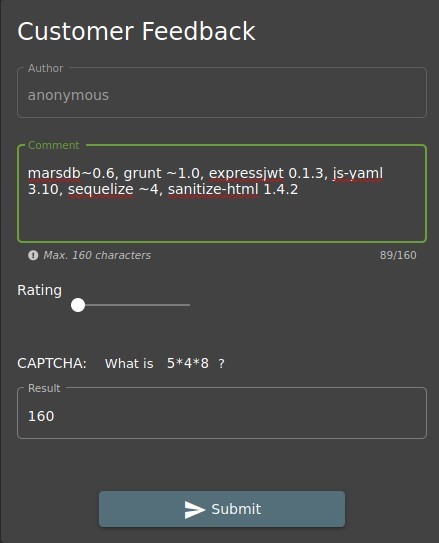
Now we just have to fill out the customer feedback form and hit submit!

Prevention and Mitigation Strategies:
OWASP Vulnerability Disclosure Cheat Sheet
Lessons Learned and Things Worth Mentioning:
- CVSS scores are a real time saver.
- There is at least one other library in the package.json.bak file that will help out in a later challenge, so be sure to check them all to save yourself some time down the road.