Challenge:
Name: Login Support Team
Description: Log in with the support team’s original user credentials without applying SQL Injection or any other bypass.
Difficulty: 6 star
Category: Security Misconfiguration
Expanded Description: https://pwning.owasp-juice.shop/part2/security-misconfiguration.html
Tools used:
Keepass2, keepass2john, johntheripper
Resources used:
https://tzusec.com/tag/keepass2john/
Methodology:
This challenge was completed out of order. I’ve been going sequentially by the star ratings thus far, but the .kdbx file I downloaded during my Poison Null Byte data acquisition spree taunted me every time I opened up my Juice Shop folder, so I decided to solve this challenge, I just wanted to move that file from the “Active Challenges” folder to the “Completed Challenges” folder.
To start, visit the FTP page and, using the Poison Null Byte trick, steal the file named “incident-support.kdbx”.


Now that we have the KeePass2 file, it’s time to crack the master password. Translating the file into a format we can hit with johntheripper is easy, as there’s a tool specifically written to accomplish that task.
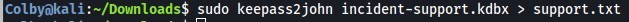
Then it’s just a matter of applying johntheripper and RockYou to crack the password
![ColbyökaU:-/Down10ads$ john --wordlist=/home/colby/tools/wordlists/rockyou.txt
/home/Colby/Hack/Juice\ Shop/support. txt
Created directory: /home/colby/. john
Jsing default input encoding: UTF-8
Loaded 1 password hash (Keepass [SHA256 AES 32/64])
Cost 1 (iteration count) is 1 for all loaded hashes
Cost 2 (version) is 2 for all loaded hashes
Cost 3 (algorithm [ø=AES, 1=TwoFish, 2=ChaCha]) is for all loaded hashes
Nitt run 4 OpenMP threads
Press 'q' or Ctrl-C to abort, almost any other key for status
og DONE (2020-11-16 13:30) øg/s 1644Kp/s 1644KC/s 1644KC/s
..*7 i Vamos !
Session completed
Col byokal i : —/Down10ads$](https://curiositykillscolby.com/wp-content/uploads/2020/12/image-15.jpeg?w=641)
Ugh. Unicode. OK, whatever. 6 star challenges ain’t sh*t.
![Login
Email
support@juice-sh.op
Password
Forgot your password?
Log in
C] Remember me
G Log in with Google
Not yet a customer?](https://curiositykillscolby.com/wp-content/uploads/2020/12/image-16.jpeg?w=668)
… but no login occurred. Time to start looking at the code to see what secrets it holds.

While searching the main JavaScript file in search of “support”, this peculiar string appears.
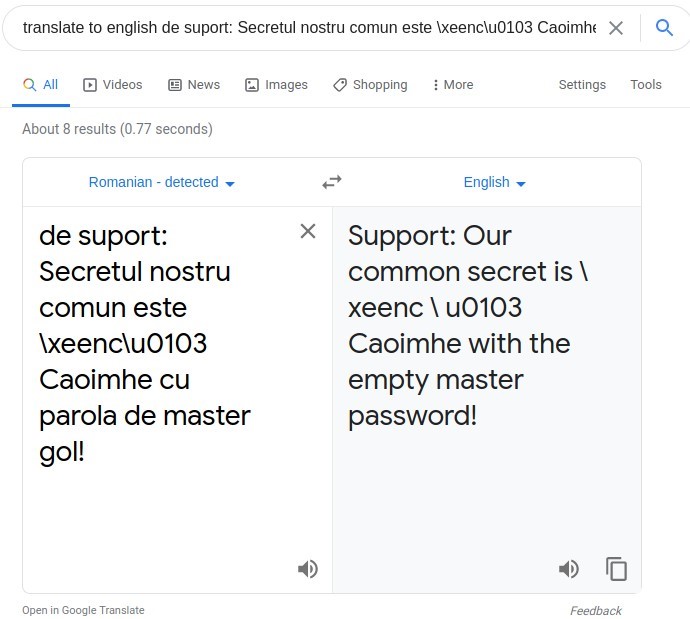
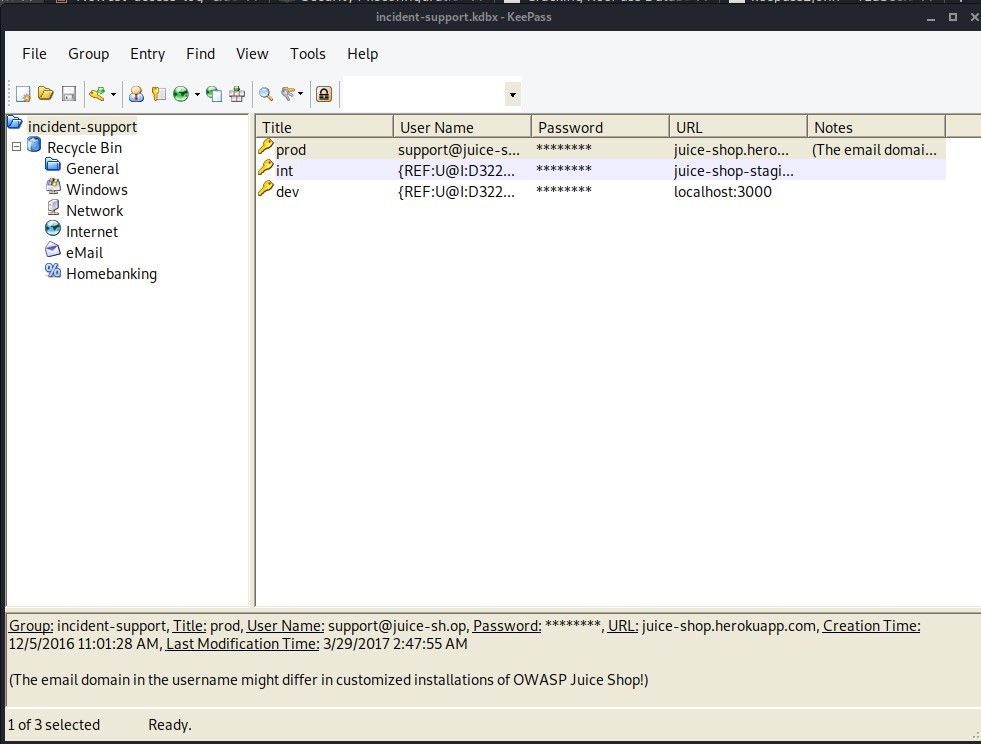
What on earth is a Caoimhe?
![Caoimhe
From Wikipedia, the free encyclopedia
Caoimhe K(W)EE-va; Irish: ['ki:vja]), anglicised Kiva, Queeva in the Republic of
Ireland or Keeva in Northern Ireland, is an Irish feminine given name derived from Irish
caomh (Old Irish cöem) "dear; noble" from the same root as the masculine name
Caoimhin (Kevin).
As of 2014, it was ranked 19th most popular name among female births in Ireland.[21](https://curiositykillscolby.com/wp-content/uploads/2020/12/image-17.jpeg?w=650)
Irish girls. My old nemeses.
But what Irish girl is on Juice Shop? Admittedly, this is where the Solutions Guide came in handy. It turns out that in the carousel of photos in the “About Us” tab, a lone redhead’s image appears.

After finding where that image was stored using Inspect Element and downloading it, I then tried to use it as the key file for the incident-support.kdbx file.
Viola!
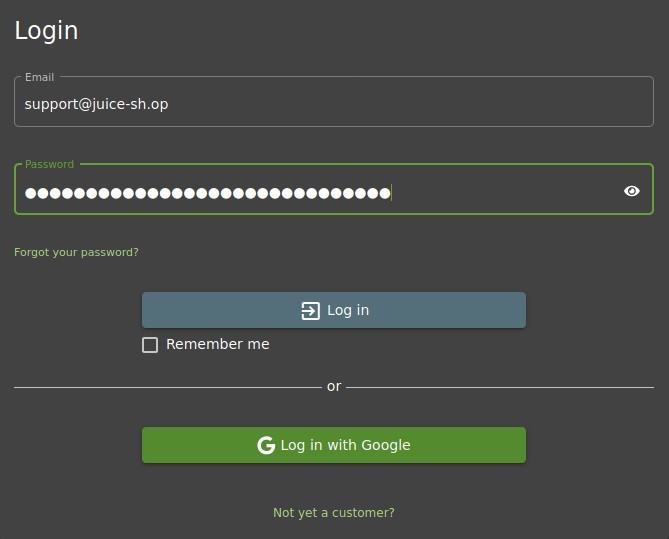
Thankfully KeePass2 lets you double click on passwords to copy them, rather than making me type out that whole string.
Prevention and Mitigation Strategies:
OWASP Authentication Cheat Sheet
Lessons Learned and Things Worth Mentioning:
- In hindsight only, I adore problems that grab my attention and don’t let go. For whatever reason, I saw the KeePass2 .kdbx file and just couldn’t stay away from this challenge. I immediately decided I wanted to know how hard it would be to break into that file. Now I know, and feel much better about my password manager. Without getting the master password or key file via KeeFarce, this was a real hassle in the best possible way.
- I don’t particularly like using the Solutions Guide as a crutch, but like I said in the first post, this is about learning more than demonstration of mastery. I’m a solid 3.5-4 star challenge hacker, and for having never even used nmap or Burp Suite four months ago that isn’t nothing.