Challenge:
Name: Leaked Access Logs
Description: Dumpster dive the Internet for a leaked password and log in to the original user account it belongs to. (Creating a new account with the same password does not qualify as a solution.)
Difficulty: 5 star
Category: Sensitive Data Exposure
Expanded Description: https://pwning.owasp-juice.shop/part2/sensitive-data-exposure.html
Tools used:
Burp Suite, FoxyProxy
Resources used:
Methodology:
The expanded description for this challenge is borderline explicit in how to begin this challenge. It mentions “a very popular help platform for developers”. Soooo Stack Overflow. After (checking the first solution guide bullet point to get the correct tag and…) a brief search, a pair of questions popped out at me. From spending so much time with the Developer Backup, I knew that “morgan” was a part of Juice Shop.

The Pastebin link lined up perfectly with another part of the expanded description, which mentioned “a platform often used to share data quickly”.
![PASTEBIN
GO
Untitled
—i A GUEST
JAN 27TH, 2019
2,229
API
TOOLS
NEVER
FAQ
Not a member of Pastebln yet? Sign up, it unlocks many cool features!
raw download clone embed
f SHARE
"WEE'
print report
Apache Log 57.36 KB
169.228.10.248
"http : //localhost
safari/537 .36"
169.228.10.248
: 11 .
•15 +9906] "GET /rest/admin/application-contiguration HTTP/I.I" 299 9253
: 30ß0/"
"Mozi11a/5 . e
: 11 .
"Mozi11a/5.e (Windows NT 10.9; Win64;
169.228.10.248
"http : //localhost
safari/537 .36"
169.228.10.248
"http : //localhost
safari/537 .36"
169.228.10.248
"http : //localhost
: 3060/"
"Mozi11a/5. e
: 30ß0/"
"Mozi11a/5 . e
: 3060/"
"Mozi11a/5. e
(Windows NT 10.9; Win64; x64) ApplewebKit/537.36 (KHTML, like Gecko) Chrome/71.9.3578.98
•15 +9906] "GET /rest/admin/application-version HTTP/I.I" 269 28 "http://localhost:3099/"
x64) ApplewebKit/537.36 (KHTML, like Gecko) Chrome/71.9.3578.98 safari/537.36"
•15 +9906] "GET /rest/admin/application-contiguration HTTP/I.I" 304
(Windows NT 10.9; Win64; x64) ApplewebKit/537.36 (KHTML, like Gecko) Chrome/71.9.3578.98
"GET HTTP/I.I" 2߀ 570
(Windows NT 10.9; Win64; x64) ApplewebKit/537.36 (KHTML, like Gecko) Chrome/71.9.3578.98
•15 +9906] "GET /rest/admin/application-contiguration HTTP/I.I" 304
(Windows NT 10.9; Win64; x64) ApplewebKit/537.36 (KHTML, like Gecko) Chrome/71.9.3578.98](https://curiositykillscolby.com/wp-content/uploads/2020/12/image-133.jpeg?w=1010)
Knowing that I was searching for a password, and also that the password reset link contains the word “current”, I searched the paste file and found both the current and new passwords for an unknown user.
![225.
161.194.17 .193
+9906] "GET
. .k8 HTTP/I.I" 401 39 "http://10ca1host:3ß@9/"
Nexus 5X) ApplewebKit/537.36 (KHTML, like Gecko) Chrome/71.ß.3578.99 Mobile
"Mozi11a/5.e (Linux; Android 8.1.9;
safari/537 .36"](https://curiositykillscolby.com/wp-content/uploads/2020/12/image-128.jpeg?w=919)
Then it was a matter of setting up a Burp Suite Intruder Sniper attack to try a password spraying attack.

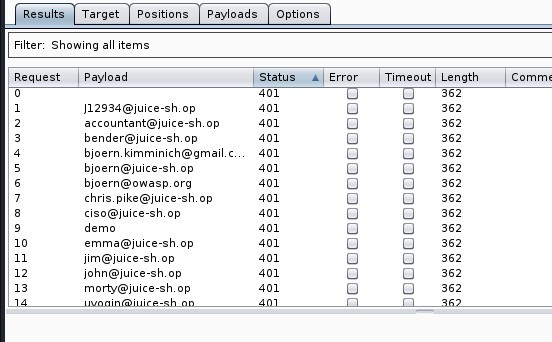
No luck. OK, back to the paste to see if something’s wrong there.

The “new” and “repeat” fields were filled in differently, meaning that the “current” password was almost certainly still the current password.
![Dashboard
Target
Payloads
Repeater
Options
Sequencer
Decoder
Comparer
Extender
Project
Target
ositio
O Payload Positions
Configure the positions where payloads will be inserted into the base request The attacktype determines the v,
Attack type Sniper
1 POST /rest/user/login HTTP/I.I
Host: local host 3000
User-Agent: MoziIIa/S.O (X
11; Linux x86 64;
application/ j son, text/ plain,
4 Accept
S Accept -Language: en-lJS,
Accept -Encoding: gzip, deflate
7 Content -Type: application/ j son
Content -Length: 49
Origin: http
// I Ocal host 3000
10 Connection: close
Referer: http://localhost : 3000/
rv.78.o)
Gecko,'20100101 Firefox,'78.o
12 Cookie: language=en; welcomebanner status=dismiss;
cookieconsent status=dismiss,
cont]
Q9ushYt NUXHVuLhkt 91QTbcms3FzinfvspHzu6t1 vycbx1g6C8Ziqj
=G-e3H196hqr0LNffAAAD
gj im@j uice-sh.0pS
14 {"email
password
Fg1L6t '61](https://curiositykillscolby.com/wp-content/uploads/2020/12/image-131.jpeg?w=659)
And yet it was not. The percent signs, however, indicate that the passwords I had scraped from the paste file were URL encoded, so I used Burp Suite’s Decoder to decode the password back into plain text.
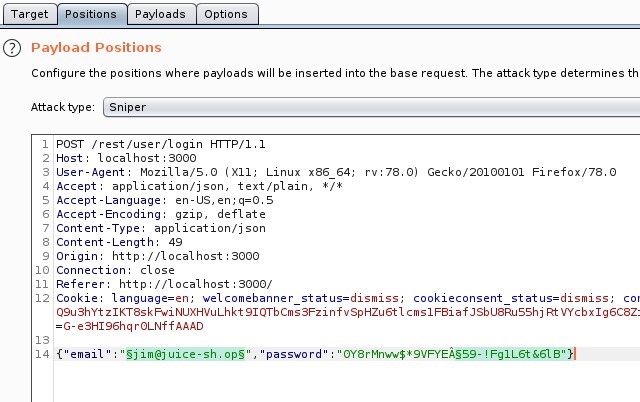
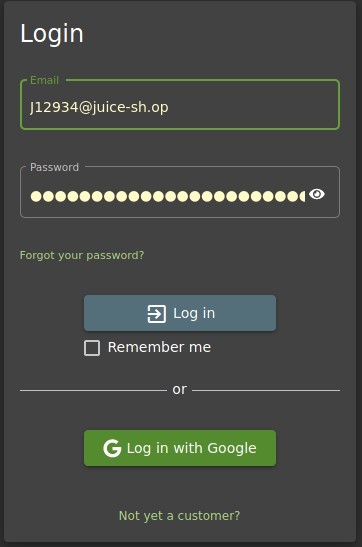
Of course one of the encoded characters would be the delimiter for Burp’s Intruder. With Burp off the table, I began manually cycling through the user table’s email addresses, using the login form until I found the right email address.

Prevention and Mitigation Strategies:
OWASP Credential Stuffing Prevention Cheat Sheet
Lessons Learned and Things Worth Mentioning:
- Always check for URL encoding.
- Sometimes all it takes is a small hint above the expanded description to make the rest of the challenge come together.