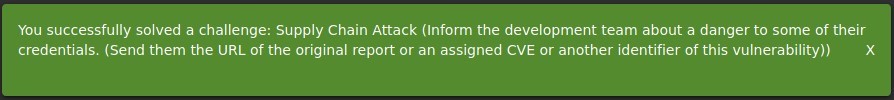
Challenge:
Name: Supply Chain Attack
Description: Inform the development team about a danger to some of their credentials. (Send them the URL of the original report or an assigned CVE or another identifier of this vulnerability)
Difficulty: 5 star
Category: Vulnerable Components
Expanded Description: https://pwning.owasp-juice.shop/part2/vulnerable-components.html
Tools used:
None
Resources used:
Methodology:
In the expanded description for this challenge there are three clues: The developers, not the customers, are the target of this attack, this is simply a research challenge, and having access to the Developer Backup will save time.
Knowing roughly what a supply chain attack is, how severe they are, and also having spent quite a bit of time during previous challenges finding vulnerable libraries in the developer’s backup file, I had a fairly short list of possible culprits.
After clicking on the vulnerability to check it out, I found two listed posts describing the issue and its mitigation. The vulnerability is apparently so bad that it is recommended that elsint-scope should be removed from all projects entirely, and it’s easy to understand why. Automatically downloading malware from pastebin coupled with remote code execution is a scary combination.


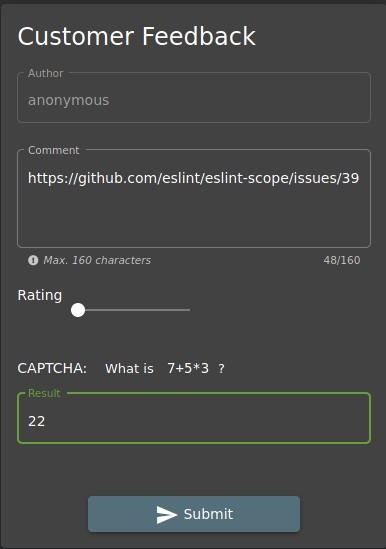
Here I had a touch of trouble figuring out what the challenge solution format was, but as I was certain I’d found the right vulnerability I didn’t feel too bad about checking the Solution Guide to find out what to enter into the feedback form.
Prevention and Mitigation Strategies:
OWASP Vulnerable Dependency Management Cheat Sheet
Keep up to date on vulnerabilities found in the libraries you’re using. When one is found to be as vulnerable as eslint-scope was, do whatever is necessary to immediately remove it from your projects. A quick and easy way to determine the severity of listed vulnerabilities is to check the CVSS score. If it’s a 9, remove the package. If it’s a 4, maybe it’s not quite as urgent, but should still be updated to a new version or replaced in a timely manner.