Challenge:
Name: Login MC SafeSearch
Description: Log in with MC SafeSearch’s original user credentials without applying SQL Injection or any other bypass.
Difficulty: 2 star
Category: Sensitive Data Exposure
Expanded Description: https://pwning.owasp-juice.shop/part2/sensitive-data-exposure.html
Tools used:
None.
Resources used:
None.
Prerequisite challenges for this methodology:
If you don’t want to complete those two challenges right now, you can easily guess the piece of information they’re used to gather.
Methodology:
This is one of my favorite challenges, because it’s completely absurd. In the expanded description this image appears:

That looks an awful lot like YouTube’s interface. Time to do some OSINT gathering by watching the video.
At 0:33 we get this gem:
“But then how do you remember is the question that I get
I say why not use the first name of your favorite pet?
Mine’s my dog, Mr. Noodles. It don’t matter if you know
because I was tricky and replaced some vowels with zeroes.”
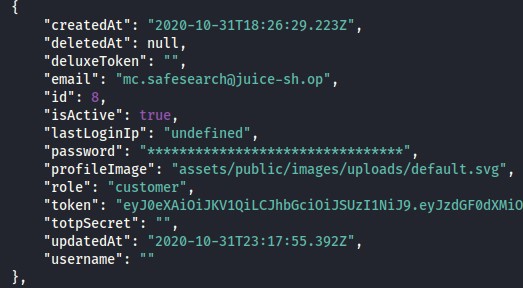
That makes it seem like the solution might be “Mr. N00dles”, doesn’t it? But what’s his email address? We need both to solve this. Harkening back to the Admin Section challenge, we found a JSON document filled with user data, so all we need to do here is go back and find MC SafeSearch’s email address, which appears to be “MC.SafeSearch@juice-sh.op”. You could also just guess.
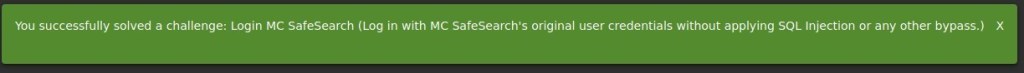
Let’s see if this works, or if we need to revisit Burp’s Intruder tab to perform another Sniper attack to cycle through possible variations of that password…

Prevention and mitigation strategies:
Take password security seriously. If you absolutely must share your passwords with someone else (spouse, shifty stranger, etc), then do not send it SMS, Email, or any other electronic medium without first encrypting the file. Generating and using an RSA key pair is a pain (not to mention getting the other person to do it), but it beats having your identity stolen.
Use unique passwords for every account you have. When I took my first security course a year ago I was one of those people who reused a few passwords over and over. Today I carry a cipher with me everywhere I go (qwertycards.com has credit card-sized unique ciphers for $5), and to keep myself from forgetting any of the dozen different password character restrictions I’ve encountered, I store all of my passwords in a password manager.
Password managers aren’t 100% secure (nothing is), either. But someone has to seriously want your passwords to use tools like KeeFarce, for KeePass2.x, successfully.
Lessons Learned:
- The more research you do in the process of completing each challenge/hack can pay dividends elsewhere. Without having the user JSON file to reference, this would have required additional effort to find MC SafeSearch’s email address.
- No sites I could find had the full lyrics to this amazing song.